PowerStore: How to Extract Self-Signed Root Certificate
Summary: Some processes require the root certificate for the PowerStore's internal certification authority (CA). This article shows how to extract that information.
This article applies to
This article does not apply to
This article is not tied to any specific product.
Not all product versions are identified in this article.
Instructions
If the PowerStore is using self-signed certificates, some processes may require the CA's root certificate. This information can be gathered and turned into a Privacy Enhanced Mail (PEM) file with the following steps.
1. Connect to the PSTCLI shell of the PowerStore.
2. Display the list of certificates on the PowerStore.
3. Display the contents of the external Management_HTTP certificate.
4. Identify the root certificate. This should be the certificate with no subject_alternative_names, as shown above.
5. Open a blank text file in Notepad and paste in the value of the certificate field.
6. Type -----BEGIN CERTIFICATE----- on a separate line at the top of the file.
7. Remove all line breaks from the certificate string.
8. Add -----END CERTIFICATE----- on a separate line at the end of the file.
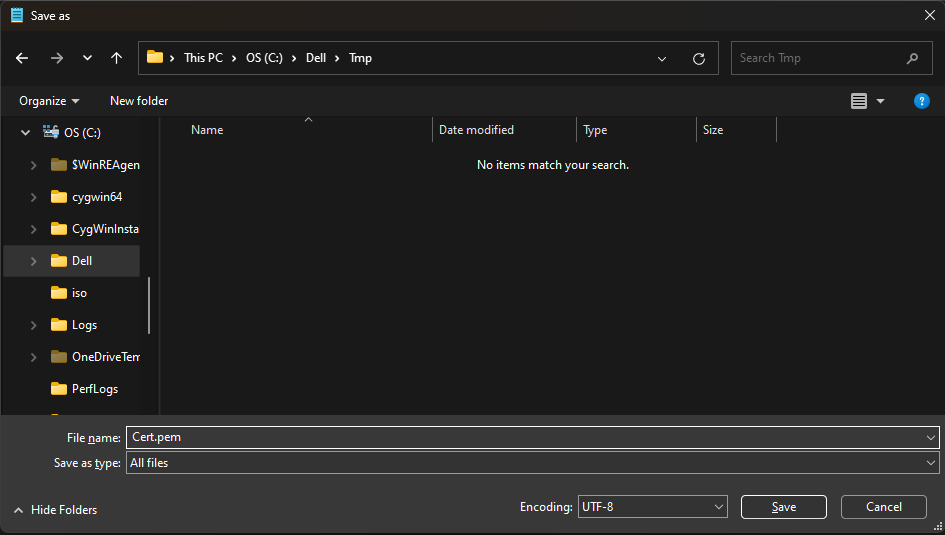
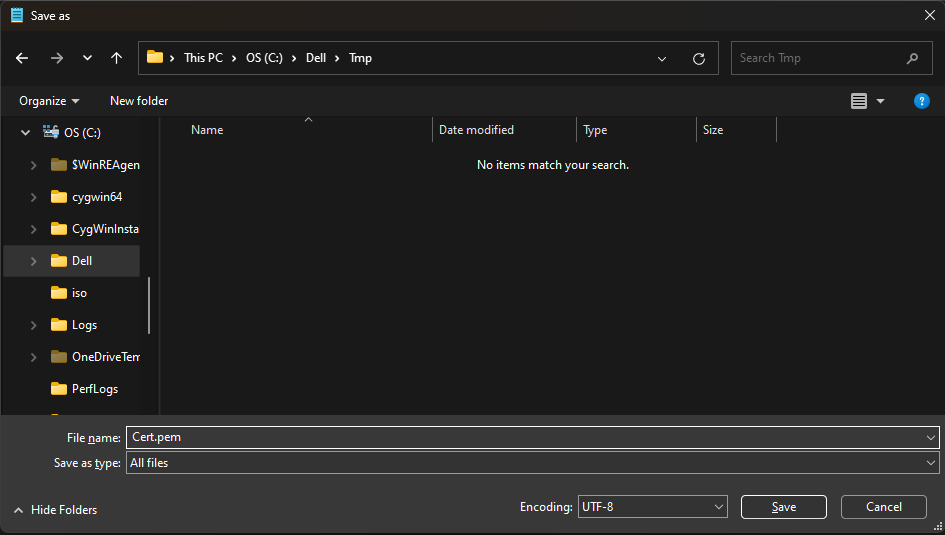
9. Save the text file as a PEM file by using <file name>.pem as its name. Select "All Files" from the Save as type dropdown list.
1. Connect to the PSTCLI shell of the PowerStore.
2. Display the list of certificates on the PowerStore.
cli> x509_certificate show # | id | type | service | is_current | is_valid ----+--------------------------------------+----------------------+------------------+------------+---------- 1 | af54dc96-a699-477a-b964-ffb4d84e867f | Server | Management_HTTP | no | no 2 | 206c6ac1-9894-44e7-8ce7-a79e40a01530 | Server | Management_HTTP | yes | yes 3 | e19110de-f58c-4558-b51a-78feca86f166 | Client | Replication_HTTP | yes | yes 4 | 3126a72e-c5c6-49fd-8588-83c7fc54286c | Server | Management_HTTP | yes | yes 5 | 4e8d100e-e0b6-41f6-8b12-b363ae79c748 | CA_Client_Validation | Replication_HTTP | yes | yes 6 | e1451f9f-dad9-41be-8871-22eb8eda98b2 | CA_Server_Validation | Replication_HTTP | yes | yes 7 | f0147daa-4565-41f9-aaba-beac477f6255 | Server | VASA_HTTP | yes | yes
3. Display the contents of the external Management_HTTP certificate.
cli> x509_certificate -id 3126a72e-c5c6-49fd-8588-83c7fc54286c show
id = 3126a72e-c5c6-49fd-8588-83c7fc54286c
type = Server
type_l10n = Server
service = Management_HTTP
service_l10n = Management_HTTP
scope = External
is_current = yes
is_valid = yes
members:
subject = 2.5.4.5=#134061613031306232643938326138306638366364396164636463313336373235653735383635636438613530353036393131636130653937626463383839376339,ST=Massachusetts,L=Hopkinton,C=US,CN=ManagementHTTP.PS1f9ce7
8ee4ef,OU=PowerStore,O=Dell
serial_number = c3a83ba91655657e
signature_algorithm = SHA256withRSA
issuer = CN=Dell EMC PowerStore CA NJ5RVJRE,O=Dell EMC,ST=MA,C=US
valid_from = 06/02/2023 08:30:09 PM
valid_to = 05/31/2028 08:30:09 PM
public_key_algorithm = RSA
key_length = 4096
thumbprint_algorithm = SHA-256
thumbprint_algorithm_l10n = SHA-256
thumbprint = 967f72eebac41c34244a71941d53b82576acaaf407088223848623961c70a651
certificate = MIIF0DCCA7igAwIBAgIJAMOoO6kWVWV+MA0GCSqGSIb3DQEBCwUAMFcxCzAJBgNVBAYTAlVTMQswCQYDVQQIEwJNQTERMA8GA1UEChMIRGVsbCBFTUMxKDAmBgNVBAMTH0RlbGwgRU1DIFBvd2VyU3RvcmUgQ0EgTko1UlZKUkUwHhcNMjMwNjAyMjAzMDA5WhcNMjgwNT
MxMjAzMDA5WjCB0DENMAsGA1UECgwERGVsbDETMBEGA1UECwwKUG93ZXJTdG9yZTEmMCQGA1UEAwwdTWFuYWdlbWVudEhUVFAuUFMxZjljZTc4ZWU0ZWYxCzAJBgNVBAYTAlVTMRIwEAYDVQQHDAlIb3BraW50b24xFjAUBgNVBAgMDU1hc3NhY2h1c2V0dHMxSTBHBgNV
BAUTQGFhMDEwYjJkOTgyYTgwZjg2Y2Q5YWRjZGMxMzY3MjVlNzU4NjVjZDhhNTA1MDY5MTFjYTBlOTdiZGM4ODk3YzkwggIiMA0GCSqGSIb3DQEBAQUAA4ICDwAwggIKAoICAQCHF1+wNWF5ogZXUVizJZBV+6xHqkEPpohzAUq+TogBiYLrW9ryWjCSL+cj2jJ0j2CwjP
muOskjazPmC9Obs2kDJwVP2IcQJ6QvyMRFuQmjZac/FxjXO5V2DifiphWP/plctNSmw7FhHU7VY/znpgSQifodh1sFvIzu5Dvp1zK7CJzVhJn8We/vu655XGCmzFra1NhKU8GtqlMH04mheUZWWAYXHhXMj1LhWV+T1xPY0kuhQDXcKI4YSf8X7DV/sfRiWOBFbew8zmvJ
N5akpV6v9hmWLciePvlMb2IwTlZo8NFoO5rw7zsP1NSnNF8ovdDE7drFGKbTOu9ZtpTIDck+UW674BqBq0ZsBnqDEq++GDLQV7oKu4bO1+kD8Q7Zhi/yE7XerGU4MwrCFvPlHavlvY8wfAl8H9vR69utfN4XqzV0DqR5SWqXoBPFRc/9yE1zEY9zNBfFuEMKgzbEQV9xGm
Si9xYbHh+hsiPnQh5bbDCp6Ty/dj0s3MsiOq2meMPeRWpcfsniJDmwLZYzvkuOVT+/EfNw2aTCtESkRvlisnykYy2q+H8bgN7Qj4CzIONWxuQVQnxbJq9s1E9Sn+ZUOzg9p8+WHY1sscIj/QtjUjhzYhHuCxZvCJ8QYiNqBLRCFqQl/doa8c7F213VPHwc/TOOmFLE3RNw
TwCPlZBCpwIDAQABoyUwIzAhBgNVHREEGjAYhwRkXEwehxD9td4xdnAAAAIBRJ/zNlH8MA0GCSqGSIb3DQEBCwUAA4ICAQB4A+yNlSB3pKLNRAKDv8nqH+1KWPq+UhiVMsERfPypLmQSHdFadWhsz2ZJ9WOri/kQjBEP/al393foTQGuEZit8UCjnwQYDoi2YvFCmusrsS
QZY0IBjq9dcrk+5daR74FU8fRu+bv0MQ8A98pEClbVQZ7+FsSvBgSL+8pjuBCSGNh88h0SkLz0QcTCAwYO/Jw9AEiSf1esSWd9+MFP1GJAyYrDyz4pqEaZVA6tuQMx1bTM4X85Xo3C8uayqgXRSb3lyiBsPbjfisanU+coXPDJmSHZlURGWVgu8jLph+WwSTjQlp59a645
drrL39vEA1bJKlZMtkvfcFq4lHCIzYpw4+EfSf46wdWal5yNWblveqIQFxIb9iNXJz+CqvJRd0zevxq7tq24taSzCdiyF0zo/3LZC4+nhEhfDYdfGXtRYM6JsAEYGWutXHZBUmLUFblGOwwHMaWD4OfIsg46uD7Gu6ilv/hv2Vw9mnkfmhz00uWSlFlqObV/3ASt4I3f4n
1mDhPzd5nCgppHBpk/Qt2FGumHzbRISoE/cQlyX273zfDuLorOq3pfzCpK34jbUY0fJR30LwMVVn6ezGWgVtGdJfRE32g0rq3W82MtbDl4+DNv37RHBCSOnHoWzx8AIp6pIGhAHVzduZlFdAoMbiLXwlqtGDqS5vcTONHg6lXPpg==
depth = 1
subject_alternative_names = 100.92.76.30, fdb5:de31:7670:0:201:449f:f336:51fc
subject = CN=Dell EMC PowerStore CA NJ5RVJRE,O=Dell EMC,ST=MA,C=US
serial_number = 2508e202beb65651
signature_algorithm = SHA384withRSA
issuer = CN=Dell EMC PowerStore CA NJ5RVJRE,O=Dell EMC,ST=MA,C=US
valid_from = 06/02/2023 07:49:05 PM
valid_to = 05/16/2091 07:49:05 PM
public_key_algorithm = RSA
key_length = 4096
thumbprint_algorithm = SHA-256
thumbprint_algorithm_l10n = SHA-256
thumbprint = 6636500d82b164cb20d4468d969e050ca14ba94d7511ba2638d89ecc485456f8
certificate = MIIFdDCCA1ygAwIBAgIIJQjiAr62VlEwDQYJKoZIhvcNAQEMBQAwVzELMAkGA1UEBhMCVVMxCzAJBgNVBAgTAk1BMREwDwYDVQQKEwhEZWxsIEVNQzEoMCYGA1UEAxMfRGVsbCBFTUMgUG93ZXJTdG9yZSBDQSBOSjVSVkpSRTAgFw0yMzA2MDIxOTQ5MDVaGA8yMDkxMD
UxNjE5NDkwNVowVzELMAkGA1UEBhMCVVMxCzAJBgNVBAgTAk1BMREwDwYDVQQKEwhEZWxsIEVNQzEoMCYGA1UEAxMfRGVsbCBFTUMgUG93ZXJTdG9yZSBDQSBOSjVSVkpSRTCCAiIwDQYJKoZIhvcNAQEBBQADggIPADCCAgoCggIBAKWpvUeq7g6ln/6v+9iN9nHtOG17
CvSntzmUfcORg7FKkoYDJqznSyNvb7VJjsrKhf5sX+8rcEOmDbPU6CPT489yismZZfffW0ghuZhy4WCLFg/ljrAx2vCG2JF7j+ENWevmiz/d5rQxOKksl/LFTqAKDSVrFyuy5b50sIKRFq8a4w+EMm5HS1rKthHYYfn64xNQmn+b7s3IZpSGAT8h4pBRXKwkz+wIiqMrci
pQZHMoDjIw5vmqxWa/3g/TXdWnST+yu78mH1oL+EBZgU8FOzHefi0RXBekQy7jm+T7l6uU+aER7JwYZt1RkZbUtUrptoFkeH8TYdgfZtxi2kIzFSHlcrJTENgv3uFJ/8EoVbWDzrizACLFFS4y3Mv26WrXH3ZHej2Nc+0zo6rJmBrIfxqqGjEUPQyEbcHRCSPcsS9yOPRu
bSd1jINDNUZO2SOkzaHIhR9ZOizTsG+yQgwVf8UKeG9RxThE8RvkBJoN4t3RNgY5HmT1ggcq1WV/TwuxQKANH/k85COCya+5ggmYo1/0XrbntbUK6DCrvthxbGKBPQDseC3GxcaUmcca8lstC5q02OxaFiNp4DIpwQjUWUhIFxXVAFcbT6ZXg2SqJEZsMAxGYIEb2HIVwk
FDfKnr3fpUjx+0tr+Z3rsRiK5qjYvCwhta64z3ijyK3DTV0F9PAgMBAAGjQjBAMA8GA1UdEwEB/wQFMAMBAf8wDgYDVR0PAQH/BAQDAgEGMB0GA1UdDgQWBBSxnEJxl8dWerjUl9Vtj0mKG1FvEDANBgkqhkiG9w0BAQwFAAOCAgEAQzU1mhssT5OBD9gYpQ5bpPdgrFkp
qckn2FY6I9RnSELeCS9LqmYKt68I9omFb4fkpuErSj9Z9RcIPM5eI2M7IqX9c5U6sd4Dw0JxUBOydewQdir6jrxIiaYs0GN7Wv8dVAUyhiodHb6PsWPqlM9XR/gdqxsVEdHCH+rg42oncuSxdC2lzxqLEUXBafFcnT7b2pq27CjKRqSNF7tSTthBKiHpiWC8EH+HSyO7Nv
PbMisxFahNL01jKZnUtvolMh/wV1/xeNgYvHUSRb0wnoAOwi3xQbXzjnBz5EjQcbmb66GXB0unvN18abJKbNnoqFSOkcoBpucX1tANsO7TcSIg9fdwfzhzVpDh+b1gZKqLTbPcJuFB0kMa3kvB/yt00wxh84n0j8ZfCCncaSg+zKtTW8cy75qzJEeuLP/PKIifw9Xj10US
cOOe/9VWK9NAo986uUV0WzMDF/2LliDhNAoA8mb/cgqxUv1yikUfUiOc2VPAgcnepk+faZNU/nFJ7dkUhgbw53ql1Pr8vPJPnt6NHxjyTCycGZn3XijW7JYZNbcJ1xTCu94PxRupsdncM64XQOPl/XJAMqHBWVbByEASmRemrc8BJ4DgvSPKdh1OjfazYCAxlyni5pasUB
qDB01shi53AWyOhj2xABr+FyhR6G4XDNJ6VnjnHlxpUGEoSx8=
depth = 2
subject_alternative_names =
4. Identify the root certificate. This should be the certificate with no subject_alternative_names, as shown above.
5. Open a blank text file in Notepad and paste in the value of the certificate field.
certificate = MIIF0DCCA7igAwIBAgIJAMOoO6kWVWV+MA0GCSqGSIb3DQEBCwUAMFcxCzAJBgNVBAYTAlVTMQswCQYDVQQIEwJNQTERMA8GA1UEChMIRGVsbCBFTUMxKDAmBgNVBAMTH0RlbGwgRU1DIFBvd2VyU3RvcmUgQ0EgTko1UlZKUkUwHhcNMjMwNjAyMjAzMDA5WhcNMjgwNT <shortened for space> 1mDhPzd5nCgppHBpk/Qt2FGumHzbRISoE/cQlyX273zfDuLorOq3pfzCpK34jbUY0fJR30LwMVVn6ezGWgVtGdJfRE32g0rq3W82MtbDl4+DNv37RHBCSOnHoWzx8AIp6pIGhAHVzduZlFdAoMbiLXwlqtGDqS5vcTONHg6lXPpg==
6. Type -----BEGIN CERTIFICATE----- on a separate line at the top of the file.
-----BEGIN CERTIFICATE----- MIIF0DCCA7igAwIBAgIJAMOoO6kWVWV+MA0GCSqGSIb3DQEBCwUAMFcxCzAJBgNVBAYTAlVTMQswCQYDVQQIEwJNQTERMA8GA1UEChMIRGVsbCBFTUMxKDAmBgNVBAMTH0RlbGwgRU1DIFBvd2VyU3RvcmUgQ0EgTko1UlZKUkUwHhcNMjMwNjAyMjAzMDA5WhcNMjgwNT
7. Remove all line breaks from the certificate string.
-----BEGIN CERTIFICATE----- MIIFdDCCA1ygAwIBAgIIJQjiAr62VlEwDQYJKoZIhvcNAQEMBQAwVzELMAkGA1UEBhMCVVMxCzAJBgNVBAgTAk1BMREwDwYDVQQKEwhEZWxsIEVNQzEoMCYGA1UEAxMfRGVsbCBFTUMgUG93ZXJTdG9yZSBDQSBOSjVSVkpSRTAgFw0yMzA2MDIxOTQ5MDVaGA8yMDkxMDUxNjE5NDkwNVowVzELMAkGA1UEBhMCVVMxCzAJBgNVBAgTAk1BMREwDwYDVQQKEwhEZWxsIEVNQzEoMCYGA1UEAxMfRGVsbCBFTUMgUG93ZXJTdG9yZSBDQSBOSjVSVkpSRTCCAiIwDQYJKoZIhvcNAQEBBQADggIPADCCAgoCggIBAKWpvUeq7g6ln/6v+9iN9nHtOG17
8. Add -----END CERTIFICATE----- on a separate line at the end of the file.
-----BEGIN CERTIFICATE----- MIIF0DCCA7igAwIBAgIJAMOoO6kWVWV+MA0GCSqGSIb3DQEBCwUAMFcxCzAJBgNVBAYTAlVTMQswCQYDVQQIEwJNQTERMA8GA1UEChMIRGVsbCBFTUMxKDAmBgNVBAMTH0RlbGwgRU1DIFBvd2VyU3RvcmUgQ0EgTko1UlZKUkUwHhcNMjMwNjAyMjAzMDA5WhcNMjgwNT<shortened for space>1mDhPzd5nCgppHBpk/Qt2FGumHzbRISoE/cQlyX273zfDuLorOq3pfzCpK34jbUY0fJR30LwMVVn6ezGWgVtGdJfRE32g0rq3W82MtbDl4+DNv37RHBCSOnHoWzx8AIp6pIGhAHVzduZlFdAoMbiLXwlqtGDqS5vcTONHg6lXPpg== -----END CERTIFICATE-----
9. Save the text file as a PEM file by using <file name>.pem as its name. Select "All Files" from the Save as type dropdown list.
Affected Products
PowerStore, PowerStore 1000T, PowerStore 3000T, PowerStore 3200Q, PowerStore 3200T, PowerStore 5000T, PowerStore 500T, PowerStore 5200T, PowerStore 7000T, PowerStore 9000X, PowerStore 9000T, PowerStore 9200T, PowerStoreOSArticle Properties
Article Number: 000226316
Article Type: How To
Last Modified: 02 Jul 2025
Version: 4
Find answers to your questions from other Dell users
Support Services
Check if your device is covered by Support Services.