In previous posts, I have looked at the use of traditional and modern management solutions to provision devices and how these techniques are suited to different categories of users (persona groups) within your workforce. I then discussed how important it is to make the best first impression and how that can be achieved by optimising data and applications migration. In this post, I will be addressing one of the hottest Windows 10 topics my customers ask for help with, namely preparing the applications for migration.
Preparing applications for migration is a multi-faceted challenge and with the introduction of Windows as a Service, it needs to be revisited for each Windows 10 version upgrade. The stages required to complete one pass of this process are as follows:
1. Identify
2. Rationalise
3. Assess
4. Package/Remediate
5. Pre-provision/Deploy
6. Support
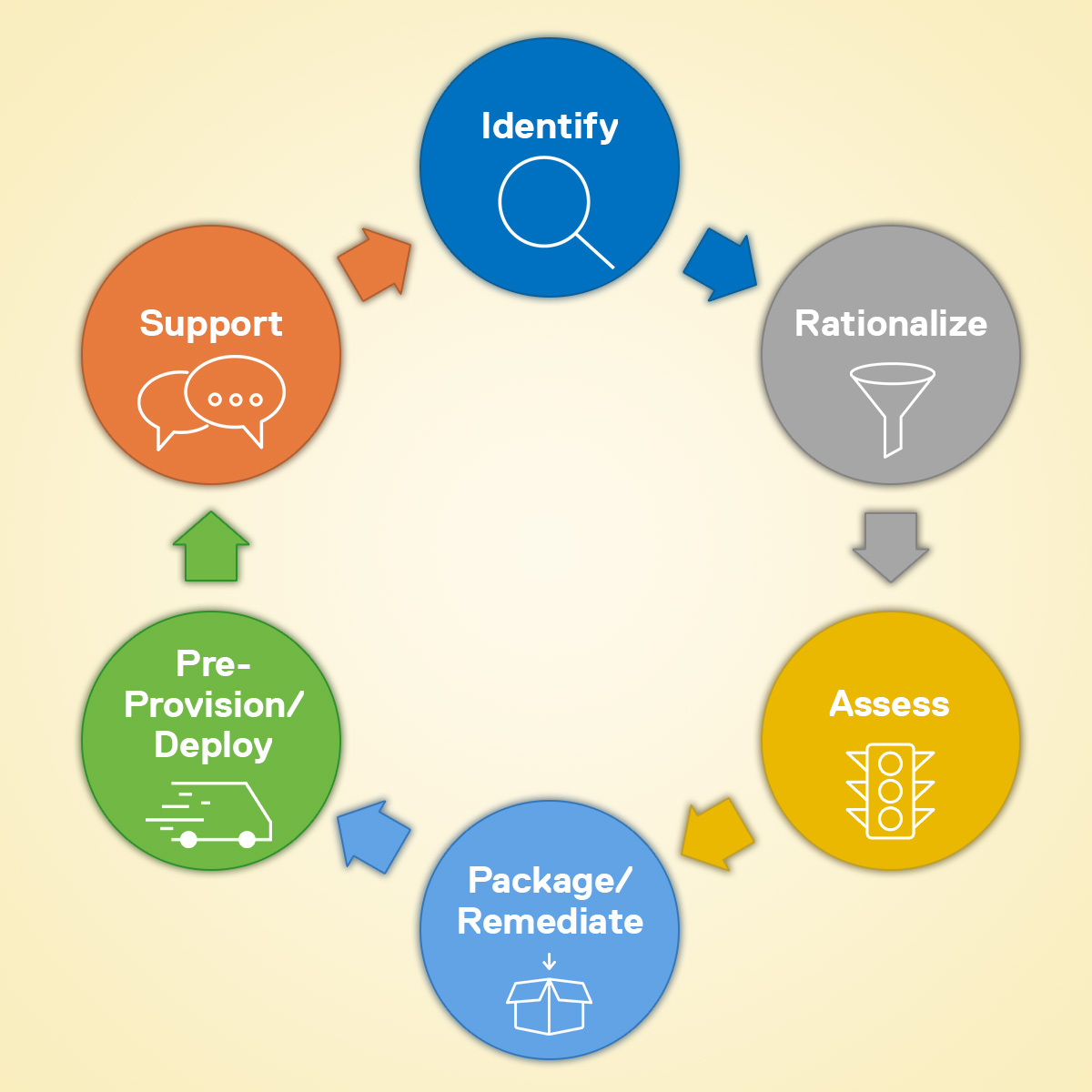
Whilst addressing each of these steps on a bi-annual or annual basis to keep pace with Windows 10 releases may seem daunting, putting the effort in on the initial migrations, and keeping the data up to date, will mean that subsequent updates are much less onerous. Adopting this rigour will yield a controlled and managed environment with valuable information and security benefits.
1. Identify
This is a two-fold task. The first is to create an inventory of all the applications currently running in your estate. Note that I did not qualify them as authorised applications yet. Many customers have suffered with application sprawl either because they have multiple versions of the same application running or because too many people have elevated privileges and have been self-installing “useful” software.
The second part of the task is to build a matrix that shows which individuals use which applications. Once you have rationalised the list, you will need to create a matrix detailing the applications for each user, including the substitutions resulting from the standardisation. This matrix, once completed will be your guide when you come to pre-provision or deploy applications in step five.
Customers address the identification challenge in several ways. Some have already implemented inventory and asset management software such as Snow Software Inventory, to monitor their environments and assist with license compliance. Others will turn to Liquidware Stratusphere UX or Lakeside Systrack as part of their desktop transformation process. Both solutions require investment both in terms of licensing and implementation costs.
Microsoft has recognised the need for this information too. They are keen to gather as much telemetry data about the global Windows 10 estate as is possible. They also understand that enterprises are only likely to connect their systems and allow this data flow if they receive something compelling in return.
Microsoft have therefore created the Desktop Analytics portal. Initially released as the Upgrade Readiness toolkit, features and capabilities have been added which justify this rebranding. There are no license fees associated with the tool although, as with everything, there are implementation costs. These are derived from the need to turn on the telemetry on Windows 7 SP1 or later devices as well as making firewall rule changes to enable that telemetry to flow to the portal.
2. Rationalise
Whichever route you choose to identify your applications, you will be presented with a list that will include more lines than you hoped for! As every step from hereon in costs money calculated on a per application basis, the more effort you expend rationalising the applications, the tighter your cost control will be. Opportunities for rationalisation are as follows:
1. Standardising on one application to do a task. For example, do you really need three different dedicated PDF readers when Chrome or Edge will do? Even “free” applications cost money to support.
2. It is not unusual to find 5-10 different versions of the same application where the patching and management solution has not been keeping pace. Standardising on one version will reduce the size of your list to a more manageable one and improve your security posture.
3. Business justify every application in the list – seize this opportunity to reduce cost and security risk.
All this guidance must be balanced by demonstrable business need. Your organisation may need tools that other entities do not. Some applications may only work when paired with certain versions of supporting add ins etc. but in general the advice holds. Furthermore, your information security team may have views on the use of legacy software or some of the applications that are harder to justify.
Talking of the security team, now would be a good time for them to re-evaluate whether the security features built into Windows 10 will meet their needs instead of third party applications. This will of course depend on whether you are implementing the Enterprise SKU or not. The business cases for continued reliance on third party disk encryption and anti-malware provision, for example, are often reassessed at this stage.
3. Assess
Microsoft cite very high levels of application compatibility (more than 90%) but the caveat is that this is for commercially available software. The compatibility of those in-house applications that are business critical, will, of course, depend on how well your development team stuck to the rules.
So what options exist to quantify the risk?
Microsoft’s Desktop Analytics will help you with the commercial off-the-shelf (COTS) software. It can inform you that version X of the application is already running elsewhere by someone else who is providing the telemetry data. The more people that use the telemetry-based system, the more informative it gets – we are all, after all, in this together. The telemetry can also tell you about Office add-ins and their compatibility with Office 365 Pro Plus as well.
The challenge with telemetry-based systems is that someone else must be running your software to give you a reading. However, in-house software tends to be just that and therefore there is no one else to rely on.
So what alternatives do you have?
The first option is to manually test the software on a build of Windows 10. This is labour intensive and will only test the components of the product that the test script exercises. With a small number of applications to test, this may be acceptable. However, most people reading this blog probably have more than one or two applications to test, so what then?
Option two is to use an automated testing solution such as Citrix AppDNA or Flexera Test Center. Extending this, many organisations, including Dell, offer services based on these tools that enable you to outsource the testing process and any subsequent remediation and repackaging tasks. These tools and services do not address underlying code issues, they simply use application packaging processes to address any incompatibilities.
For example, many customers will be standardising on 64-bit Windows 10 systems as part of their upgrade, if they had not made this change earlier. 64-bit Windows cannot run the 16-bit code that was often present in 32-bit applications, meaning that the application will fail. The test products and services mentioned above can detect this incompatibility, but no amount of re-packaging can fix this, it requires code changes.
Typically, output from the testing tool is in the red-amber-green format. Red indicates a failure that may well need a new version. Amber indicates that there is a way to remediate the package and green suggests that the package is ready for user acceptance testing. The only deviation from this is testing for 64-bit compatibility, which is either red or green – there is no halfway here.
4. Package/Remediate

Having rationalised your application estate, you may well have decided that you are going to continue to use “ApplicationX” but you have previously been unable to upgrade to its latest version as it was only compatible with Windows 10, or perhaps you have made the switch to the 64-bit version of it. To deploy it widely, you will need to package it so that your Electronic Software Distribution (ESD) tool can deliver it.
This has several benefits:
1. It will always be installed in the same way by the tool.
2. It does not require an engineer to touch each device.
3. The tool can be used to update the application, reducing the likelihood of application version sprawl and the inherent security vulnerabilities that brings.
4. The users can be allowed to initiate the install from an application store without raising a helpdesk ticket, subject to licensing constraints.
5. The tool can be defined as a Trusted Installer when using Windows Defender Application Control enabling you to further improve your security posture.
Applications are typically packaged as MSIs for tools such as Microsoft’s ConfigMgr, although some will be sequenced for use with application virtualisation solutions such as Microsoft’s App-V or VMware’s ThinApp.
There is a new kid on the block, MSIX. This is Microsoft’s attempt to make application installation as simple on a Windows device as it is on a mobile device. Support has been added to ConfigMgr Current Branch build 1806 onwards. This format looks to have some good attributes and may well be important for the future.
As suggested in the Assess section above, remediation of amber applications takes the form of modifying the existing package, perhaps to change a setting, or to add a helper file to make the application compatible with Windows 10.
Engaging with Dell’s Global Applications Packaging team, will deliver a service that can assess, remediate existing packages as well as creating new packages (MSI, App-V and ThinApp today with MSIX coming soon) all on a per application basis. Our packaging service works to a greater than 95% first time right packaging and we offer a warranty to address any issues that our team might introduce.
Finally, Microsoft have recently announced their Desktop App Assure programme via FastTrack where they offer to help customers struggling with application compatibility including those tricky line of business applications where you no longer have the source code. They have even made the shortcut easy to remember: https://aka.ms/800appcompat
5. Pre-provision/Deploy
I have already discussed the benefits of using an ESD tool such as ConfigMgr to deploy your applications and in my previous post, Windows 10 Migration: Best Practices for Making a User’s First Impression Great, I discuss the benefits of pre-provisioning and how Dell can help you with our factory configuration services using either ConfigMgr or Workspace ONE.
To recap, application deployment via a tool such as ConfigMgr or Workspace ONE gives you the ability to centrally control and manage your application estate, minimising application sprawl, whilst keeping things up to date to enhance your security posture. It also enables your users to install applications using an application store in similar fashion to the way they do on their mobile device.
Pre-provisioning is the deployment of the applications to the device prior to it being issued to the user. This can save bandwidth and will certainly enhance the day one user experience. However, it relies on the user application matrix discussed in the Identify section above. This then needs to be captured into the tooling such that it knows which applications are used by whom. Finally, it is necessary to assign the device to its new owner at build time, which may not suit every organisation.
6. Support

Support is critical. Software applications, presented as packages, represent an asset or configuration item. They will inevitably need patching and updating, as business needs change, or as the vendor fixes an issue or releases new functionality. With the change to the way Windows 10 is released (Windows as a Service), this cycle will be ongoing.
Windows as a Service
Windows as a Service is Microsoft’s term for the twice-yearly release of Windows 10 builds, typically released in spring and autumn. It was clear that new features would be added with each new release, but less well understood was the potential for features to be removed.
This removal is usually triggered by the lack of interest in the capability – an example recently (1809) was the removal of Business Scanning (AKA Distributed Scan Management) as there was no hardware vendor support for it. Alternatively, a feature can be superseded such as the Hologram app which has been replaced by the Mixed Reality Viewer.
This addition and removal of features can impact application compatibility, meaning that the roll-out of each build of Windows 10 should be considered a mini-migration. It is not as daunting as the initial move from Windows 7 to Windows 10 but still worth checking those business-critical applications.
 As mentioned at the start, doing all of this on a bi-annual or annual basis might seem a challenge. However, doing the hard work the first time you enter the Identify and Rationalise phases and then keeping the information up to date will allow you to become more efficient with each passing cycle.
As mentioned at the start, doing all of this on a bi-annual or annual basis might seem a challenge. However, doing the hard work the first time you enter the Identify and Rationalise phases and then keeping the information up to date will allow you to become more efficient with each passing cycle.
The Dell Services team can also undertake to do this lifecycle management for you. We can address both Windows 10 image changes and applications (compatibility and vulnerability) testing and remediation for you, every six months, to help you keep your environment up to date.
To find out more about this or any of the other services discussed in this post, please feel free to contact me.
