iDRAC: iDRAC8 firmware version 2.81.81.81: HTTP or HTTPS FQDN Connection Failures
Summary: The Dell EMC-Integrated Dell Remote Access Controller 8 (iDRAC9) firmware version 2.81.81.81 blocks HTTP or HTTPS access through Fully Qualified Domain Name (FQDN) when the FQDN is not defined as the iDRAC RAC Name. ...
Symptoms
The Dell EMC-Integrated Dell Remote Access Controller 8 (iDRAC8) firmware version 2.81.81.81 introduced HTTP or HTTPS connection changes that may impact user connections when specifying Fully Qualified Domain Name (FQDN) address. Due to these changes, iDRAC9 users may encounter connection errors, redirection, or '400 - Bad Request' errors. These connection sightings occur when the specified FQDN does not match the iDRAC 'DNSRacName' or 'DNSDomainName' values.
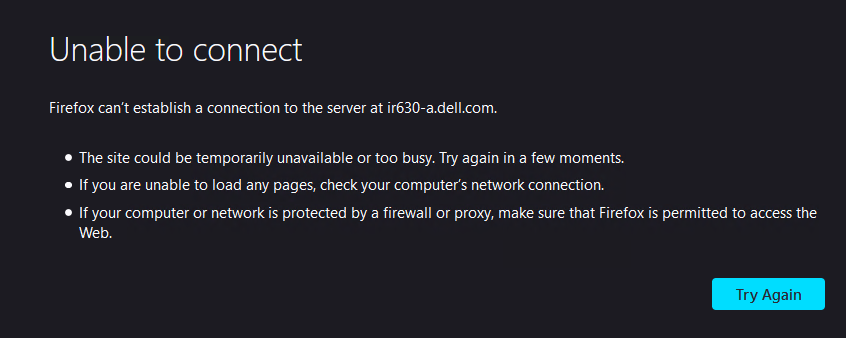
Browser Error Example:
Curl Error Example:
root@rhel7-vm:~$ curl -k https://iR630-A.dell.com/
<!DOCTYPE html>
<head>
<title>Bad Request</title>
<link rel="shortcut icon" href="data:image/x-icon;," type="image/x-icon">
</head>
<body>
<h2>Access Error: 400 -- Bad Request</h2>
<pre></pre>
</body>
</html>Cause
Resolution
By default, iDRAC8 checks the HTTP or HTTPS Host Header and compares it to the defined 'DNSRacName' and 'DNSDomainName'. When the values do not match, the iDRAC refuses the HTTP or HTTPS connection. In iDRAC8 2.81.81.81, this Host Header enforcement can be disabled with the following RACADM command:
#Disable host header check
Racadm set idrac.webserver.HostHeaderCheck 0
HostHeaderCheck value to '0' when a manual Host Record exists within the DNS environment.
When the HTTP or HTTPS Host Header check is enabled (more secure), iDRAC can be accessed using the IPv4or IPv6 address, the RAC Name, or the defined iDRAC FQDN
(DNSRacName.DNSDomainName). If end user is accessing with hostnames that iDRAC may not be aware of (such as a manual DNS entry added in DNS records), iDRAC8 2.81.81.81 firmware version introduced a new attribute 'ManualDNSEntry'. This new setting can be updated with up to four IP addresses, host names, or FQDNs to provide an allow-list of Host Headers. This ensures that incoming requests are not dropped when the HTTP or HTTPS Host Header carries one of the entries in the 'ManualDNSEntry' setting.
# Add manual entry to allow list
racadm set idrac.webserver.ManualDNSEntry 192.168.20.30
racadm set idrac.webserver.ManualDNSentry 192.168.20.30,idrac.mydomain.com
This additional configuration is required in cases when:
- The end user is using manual DNS configuration to access iDRAC (Manual DNS Host Record.
- Subject Alternative Name or Wild-card certificate is used to access the iDRAC.
- Accessing iDRAC using host IP address directly (by ISM).