IDPA: Steps to mitigate VMSA-2021-0010 (CVE-2021-21985, CVE-2021-21986) and VMSA-2021-0020 on IDPA vCenter for versions 2.5 and 2.6.x
Summary: Steps to mitigate VMSA-2021-0010 (CVE-2021-21985, CVE-2021-21986) and VMSA-2021-0010 on IDPA vCenter for versions 2.5 and 2.6.x.
This article applies to
This article does not apply to
This article is not tied to any specific product.
Not all product versions are identified in this article.
Instructions
Impact Assessment:
An automated procedure has been provided and can be run from the ACM.
Note: Dell EMC has released a new cumulative automated vCenter patch utility for versions 2.5, and 2.6.x which provides remediation for VMSA-2021-0010 and VMSA-2021-0020.
Download:
Option 1: Direct link
Note: User must be logged into Dell Support with their service account in order to download the utility.
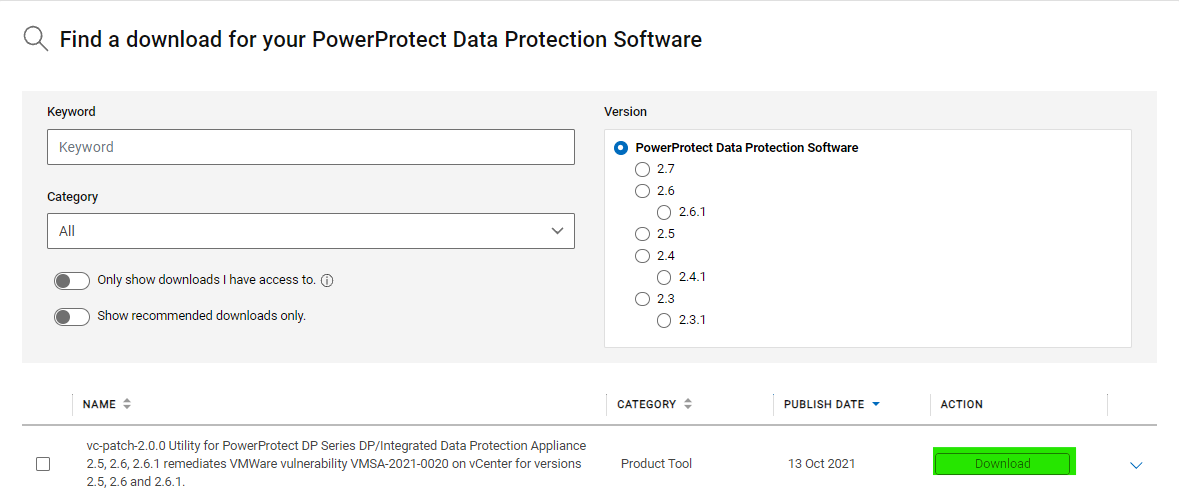
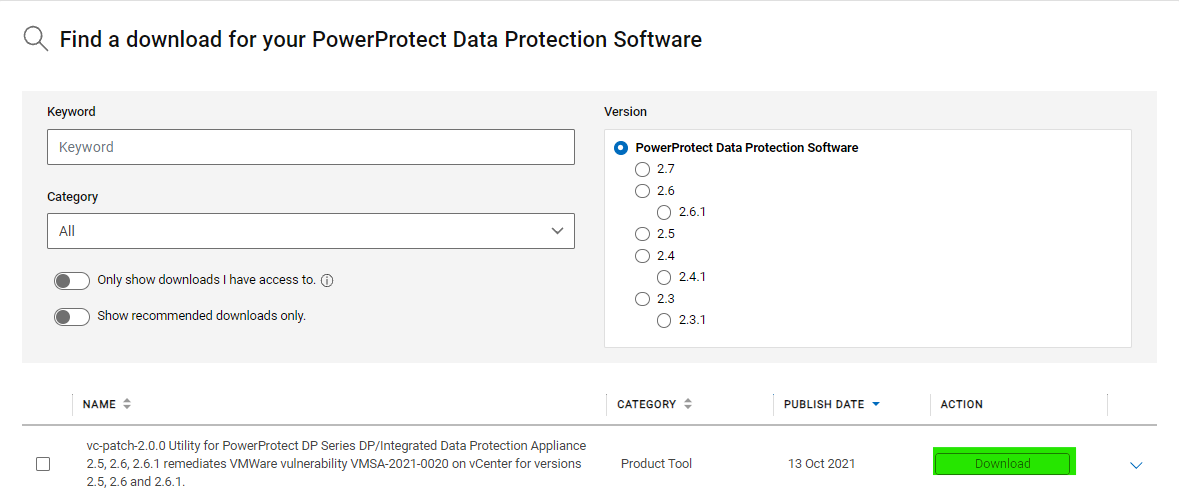
Option 2: Download via Product Page Link
Steps
Note: Extract or unzip the vc-patch-2.0.0.zip file and follow the instructions below.
- Functionality impacts are limited to IDPA Internal vCenter during the implementation of remediation procedure.
- No impact to customer backups, replications, and restore functionality.
- IDPA Internal VM (ACM, DPA, and so on) backups get impacted if they are running during the implementation of this procedure.
- The attached procedure must only be applied on IDPA versions 2.5 and 2.6.x [All Models].
- Do not use this KB for any other IDPA version.
- Remediation procedure for IDPA appliance version 2.3.x and 2.4.x is present in article 188106: IDPA: Steps to mitigate VMSA-2021-0010 (CVE-2021-21985, CVE-2021-21986) on IDPA vCenter for versions 2.3.x and 2.4.x.
- Appliances on IDPA version 2.2 must upgrade to a later version to apply remediation steps.
- This security vulnerability VMSA-2021-0010 (CVE-2021-21985, CVE-2021-21986) is expected to be addressed in an upcoming IDPA release.
An automated procedure has been provided and can be run from the ACM.
Note: Dell EMC has released a new cumulative automated vCenter patch utility for versions 2.5, and 2.6.x which provides remediation for VMSA-2021-0010 and VMSA-2021-0020.
Download:
Option 1: Direct link
Note: User must be logged into Dell Support with their service account in order to download the utility.
Option 2: Download via Product Page Link
Steps
Note: Extract or unzip the vc-patch-2.0.0.zip file and follow the instructions below.
- Copy the "vc-patch-2.0.0.jar" to "/data01" folder on Appliance Configuration Manager using an SCP client like WinSCP. SSH to ACM using an SSH client such as PuTTY using root and appliance password. Go to /data01 folder using "cd /data01" command.
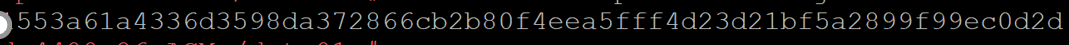
- Check sha256 sum of the file "vc-patch-2.0.0.jar" and ensure it matches with sha256sum provided in "vc-patch-2.0.0.jar.sha256" file.
- Run "java -jar vc-patch-2.0.0.jar." The patch performs prechecks and applies the vCenter patch on IDPA vCenter.

- Delete "vc-patch-2.0.0.jar" from "/data01" folder on ACM after successful execution using command "rm vc-patch-2.0.0.jar."
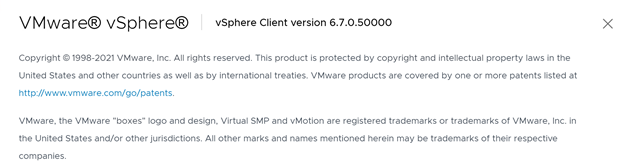
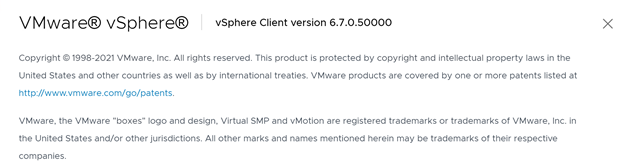
- Hit the vCenter IP in browser (like Chrome). Log in to vCenter HTML5 UI using root and password as appliance password. Click Help About VMware vSphere. You should see the following version.
- If the manual workaround to mitigate this VMSA was applied previously on IDPA 2.5 or 2.6.x, then revert the workaround steps after applying this patch. Steps to revert mitigation are present in the same mitigation KB "VMSA-2021-0010 in vCenter mitigation for IDPA 2.5 and 2.6.x_csp.docx" attached.
Products
PowerProtect Data Protection ApplianceArticle Properties
Article Number: 000187563
Article Type: How To
Last Modified: 01 Sept 2023
Version: 25
Find answers to your questions from other Dell users
Support Services
Check if your device is covered by Support Services.