Użytkownik APEX nie może wygenerować kluczy S3 z powerscale Webui
摘要: W oneFS 9.3.0.4 konto użytkownika APEX klienta jest powiązane z nową rolą BasicUser i nie może wygenerować kluczy S3 z interfejsu internetowego OneFS. Karta zarządzania kluczami nie jest widoczna dla konta APEX klienta. ...
本文适用于
本文不适用于
本文并非针对某种特定的产品。
本文并非包含所有产品版本。
症状
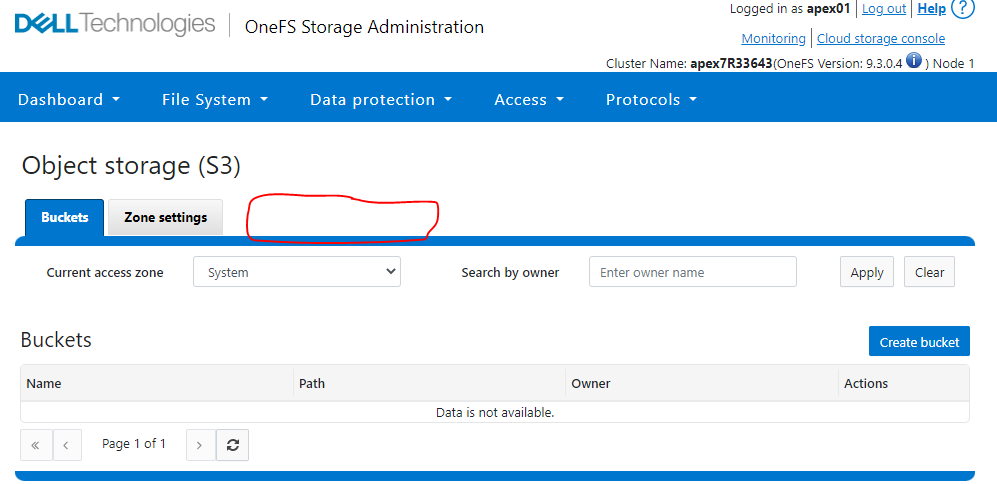
Zaloguj się do interfejsu internetowego OneFS za pomocą konta APEX klienta apex01.
Kliknij opcję Protocols -> Object Storage (S3).
Zauważysz, że karta Zarządzanie kluczami jest niewidoczna.
Przykład:
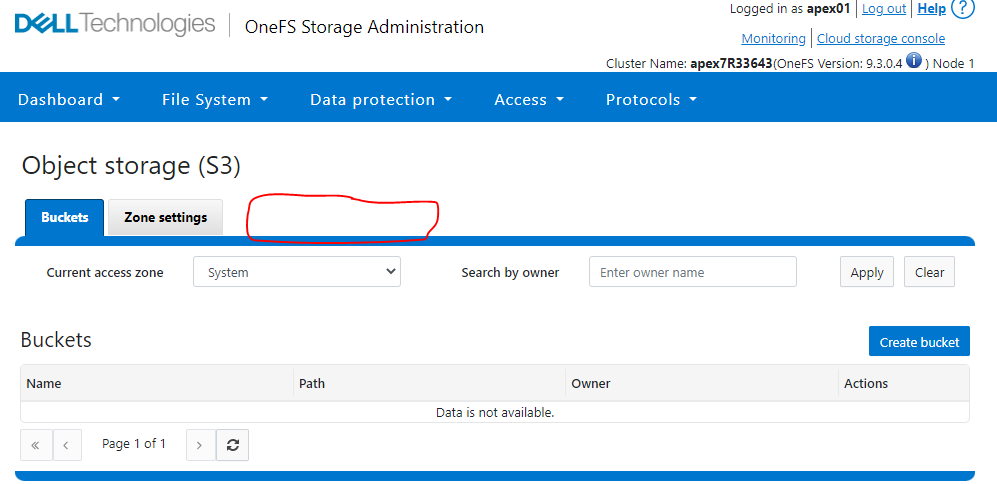
Kliknij opcję Protocols -> Object Storage (S3).
Zauważysz, że karta Zarządzanie kluczami jest niewidoczna.
Przykład:
原因
Konto klienta APEX nie ma uprawnień do generowania kluczy S3 za pomocą interfejsu internetowego OneFS.
解决方案
Obejście problemu rest API dla klienta:
1. Utwórz sesję.
2. Wygeneruj klawisz S3.
curl -kv -H "Content-type:application/json" -H "X-CSRF-Token: " -H "Referer:https://" -X POST https://:8080/platform/12/protocols/s3/mykeys -b /tmp/cookie.txt
Uwaga: Konto Klienta Apex01 nie ma dostępu do interfejsu CLI PowerScale, dlatego klient musi uruchomić obejście problemu z klientem NFS lub z wiersza polecenia systemu Windows, który ma łączność sieciową z rozwiązaniem PowerScale.
Przykład z laboratorium PowerScale:
1. Utwórz sesję:
Node_IP = nazwa użytkownika X.X.X.X
= apex01
Hasło = hasło konta użytkownika apex01
2. Wygeneruj klawisz S3:
Node_IP = wartość tokenu CSRF X.X.X
= 14762d26-e806-41c1-b310-4497afb28953 (patrz powyżej wyróżniona kolorem czerwonym z polecenia sesji tworzenia)
secret_key = wygenerowany klucz S3 ( zielony poniżej)
1. Utwórz sesję.
Monit o cmd systemu Windows:
curl --request POST --insecure 'https://:8080/session/1/session' --header 'Content-Type: application/json' --data-raw '{"nazwa użytkownika": "","hasło": "","services": ["platform","namespace"]}' -v -c /tmp/cookie.txt
Cli klienta Linux:
curl --request POST --insecure 'https://:8080/session/1/session' --header 'Content-Type: application/json' --data '{"nazwa_użytkownika": "","hasło": "","services": ["platform","namespace"]}' -v -c /tmp/cookie.txt
2. Wygeneruj klawisz S3.
curl -kv -H "Content-type:application/json" -H "X-CSRF-Token: " -H "Referer:https://" -X POST https://:8080/platform/12/protocols/s3/mykeys -b /tmp/cookie.txt
Uwaga: Konto Klienta Apex01 nie ma dostępu do interfejsu CLI PowerScale, dlatego klient musi uruchomić obejście problemu z klientem NFS lub z wiersza polecenia systemu Windows, który ma łączność sieciową z rozwiązaniem PowerScale.
Przykład z laboratorium PowerScale:
1. Utwórz sesję:
Node_IP = nazwa użytkownika X.X.X.X
= apex01
Hasło = hasło konta użytkownika apex01
apex7R33643-3% curl --request POST --insecure 'https://X.X.X.X:8080/session/1/session' --header 'Content-Type: application/json' --data-raw '{"username": "apex01","password": "","services": ["platform","namespace"]}' -v -c /tmp/cookie.txt
Note: Unnecessary use of -X or --request, POST is already inferred.
* Trying X.X.X.X:8080...
* Connected to X.X.X.X (X.X.X.X) port 8080 (#0)
* ALPN, offering http/1.1
* Cipher selection: ALL:!EXPORT:!EXPORT40:!EXPORT56:!aNULL:!LOW:!RC4:@STRENGTH
* successfully set certificate verify locations:
* CAfile: none
* CApath: /etc/ssl/certs/
* TLSv1.2 (OUT), TLS header, Certificate Status (22):
* TLSv1.2 (OUT), TLS handshake, Client hello (1):
* TLSv1.2 (IN), TLS handshake, Server hello (2):
* TLSv1.2 (IN), TLS handshake, Certificate (11):
* TLSv1.2 (IN), TLS handshake, Server key exchange (12):
* TLSv1.2 (IN), TLS handshake, Server finished (14):
* TLSv1.2 (OUT), TLS handshake, Client key exchange (16):
* TLSv1.2 (OUT), TLS change cipher, Change cipher spec (1):
* TLSv1.2 (OUT), TLS handshake, Finished (20):
* TLSv1.2 (IN), TLS change cipher, Change cipher spec (1):
* TLSv1.2 (IN), TLS handshake, Finished (20):
* SSL connection using TLSv1.2 / DHE-RSA-AES256-SHA
* ALPN, server accepted to use http/1.1
* Server certificate:
* subject: C=US; ST=Washington; L=Seattle; O=Isilon Systems, Inc.; OU=Isilon Systems; CN=Isilon Systems; emailAddress=support@isilon.com
* start date: Apr 14 20:51:44 2022 GMT
* expire date: Jul 16 20:51:44 2024 GMT
* issuer: C=US; ST=Washington; L=Seattle; O=Isilon Systems, Inc.; OU=Isilon Systems; CN=Isilon Systems; emailAddress=support@isilon.com
* SSL certificate verify result: self signed certificate (18), continuing anyway.
> POST /session/1/session HTTP/1.1
> Host: X.X.X.X:8080
> User-Agent: curl/7.79.1
> Accept: */*
> Content-Type: application/json
> Content-Length: 83
>
* Mark bundle as not supporting multiuse
< HTTP/1.1 201 Created
< Date: Tue, 21 Jun 2022 13:52:33 GMT
< Server: Apache
< X-Frame-Options: sameorigin
< X-Content-Type-Options: nosniff
< Strict-Transport-Security: max-age=31536000;
* Added cookie isisessid="eyJhbGciOiJQUzUxMiJ9.eyJhdWQiOlsicGxhdGZvcm0iLCJuYW1lc3BhY2UiXSwiZXhwIjoxNjU1ODMzOTUzLCJpYXQiOjE2NTU4MTk1NTMsIm9uZWZzL2NzcmYiOiIxNDc2MmQyNi1lODA2LTQxYzEtYjMxMC00NDk3YWZiMjg5NTMiLCJvbmVmcy9pcCI6IjEyOC4yMjEuMjI3LjMzIiwib25lZnMvbm9uY2UiOjExMTUzNzgyODM1MTU4MjE5ODk0LCJvbmVmcy9zZXNzaW9uIjoiYmZkMjVhMTMtMDNlOS00OTdhLTk2OWYtYmEwZjU1YmFhZTAzIiwib25lZnMvdWEiOiJjdXJsLzcuNzkuMSIsIm9uZWZzL3ppZCI6MSwic3ViIjoiYXBleDAxIn0K.ioRleO4O9kqDcQfzDUpjKDA9bgnpqqSYPQWJ9sDRSfkL0xI1F29YpTvnoa3uKPLZ7pE8sedkk6vpPcif1Tb7L7-9t4fG2kIXJKK7vm1VNNStUFRQMHMc1vaf8UzKwwJJKf0S_3GltOo8iRK2fdkw_bigw2xOwIHr-85YCHGJeYdFiJ2pK_CI_zYPbGAeg5hJFV7Ylci9FDRI8SDElIBe8FrvaZuiPsMloRU8oL4dxco1jAfPhjsv3YOUDXTEq7kI3xCNkKIj5PtQMjQInDz4qxHVNo9Ks7uEm2cjYotNcQ424i0tuGTe2piwdvlaiEC6WaqKo7HhuPEYqQ7vmgK_seCEb9GY6wAXw9xhpfRHb38f2qDohZj17J-6TzKU32PZ9NJutAidTFIVKH01JGOPRRdPM9oex4VH7FUFDhPAGSng1nmBEx6wk10D1LjTB36UbSQ9lkrh7y84DLZYSlJAfo3iX1_w4bZ0tZHa51K13KedLb4E3Jafjkp-MOUUwMMbjXDgxoC0IRWc2HgilDnvKaSe7R8t9vogW0E5m-0jophQD70BY7UioNu-U6CnaoFojQ-yKFS3t6ZV8i40mD3XaZKS5oeePUFWmlmPFEugziuS4dTdQY-_Myei1RhQPRydp_xFUVZyBb79yv71FLtouqB3UY0zy0qiWDip6VRCphc%3D" for domain X.X.X.X, path /, expire 0
< Set-Cookie: isisessid=eyJhbGciOiJQUzUxMiJ9.eyJhdWQiOlsicGxhdGZvcm0iLCJuYW1lc3BhY2UiXSwiZXhwIjoxNjU1ODMzOTUzLCJpYXQiOjE2NTU4MTk1NTMsIm9uZWZzL2NzcmYiOiIxNDc2MmQyNi1lODA2LTQxYzEtYjMxMC00NDk3YWZiMjg5NTMiLCJvbmVmcy9pcCI6IjEyOC4yMjEuMjI3LjMzIiwib25lZnMvbm9uY2UiOjExMTUzNzgyODM1MTU4MjE5ODk0LCJvbmVmcy9zZXNzaW9uIjoiYmZkMjVhMTMtMDNlOS00OTdhLTk2OWYtYmEwZjU1YmFhZTAzIiwib25lZnMvdWEiOiJjdXJsLzcuNzkuMSIsIm9uZWZzL3ppZCI6MSwic3ViIjoiYXBleDAxIn0K.ioRleO4O9kqDcQfzDUpjKDA9bgnpqqSYPQWJ9sDRSfkL0xI1F29YpTvnoa3uKPLZ7pE8sedkk6vpPcif1Tb7L7-9t4fG2kIXJKK7vm1VNNStUFRQMHMc1vaf8UzKwwJJKf0S_3GltOo8iRK2fdkw_bigw2xOwIHr-85YCHGJeYdFiJ2pK_CI_zYPbGAeg5hJFV7Ylci9FDRI8SDElIBe8FrvaZuiPsMloRU8oL4dxco1jAfPhjsv3YOUDXTEq7kI3xCNkKIj5PtQMjQInDz4qxHVNo9Ks7uEm2cjYotNcQ424i0tuGTe2piwdvlaiEC6WaqKo7HhuPEYqQ7vmgK_seCEb9GY6wAXw9xhpfRHb38f2qDohZj17J-6TzKU32PZ9NJutAidTFIVKH01JGOPRRdPM9oex4VH7FUFDhPAGSng1nmBEx6wk10D1LjTB36UbSQ9lkrh7y84DLZYSlJAfo3iX1_w4bZ0tZHa51K13KedLb4E3Jafjkp-MOUUwMMbjXDgxoC0IRWc2HgilDnvKaSe7R8t9vogW0E5m-0jophQD70BY7UioNu-U6CnaoFojQ-yKFS3t6ZV8i40mD3XaZKS5oeePUFWmlmPFEugziuS4dTdQY-_Myei1RhQPRydp_xFUVZyBb79yv71FLtouqB3UY0zy0qiWDip6VRCphc%3D; path=/; HttpOnly; Secure; SameSite=strict
* Added cookie isicsrf="14762d26-e806-41c1-b310-4497afb28953" for domain X.X.X.X, path /, expire 0
< Set-Cookie: isicsrf=14762d26-e806-41c1-b310-4497afb28953; path=/; Secure
< Content-Security-Policy: default-src 'self' 'unsafe-inline' 'unsafe-eval' data:; script-src 'self' 'unsafe-eval'; style-src 'unsafe-inline' 'self';
< Content-Length: 106
< Content-Type: application/json
<
{"services":["platform","namespace"],"timeout_absolute":14400,"timeout_inactive":900,"username":"apex01"}
* Connection #0 to host X.X.X.X left intact
apex7R33643-3%
2. Wygeneruj klawisz S3:
Node_IP = wartość tokenu CSRF X.X.X
= 14762d26-e806-41c1-b310-4497afb28953 (patrz powyżej wyróżniona kolorem czerwonym z polecenia sesji tworzenia)
secret_key = wygenerowany klucz S3 ( zielony poniżej)
apex7R33643-3% curl -kv -H "Content-type:application/json" -H "X-CSRF-Token: 14762d26-e806-41c1-b310-4497afb28953" -H "Referer:https://X.X.X.X" -X POST https://X.X.X.X:8080/platform/12/protocols/s3/mykeys -b /tmp/cookie.txt
* Trying X.X.X.X:8080...
* Connected to X.X.X.X (X.X.X.X) port 8080 (#0)
* ALPN, offering http/1.1
* Cipher selection: ALL:!EXPORT:!EXPORT40:!EXPORT56:!aNULL:!LOW:!RC4:@STRENGTH
* successfully set certificate verify locations:
* CAfile: none
* CApath: /etc/ssl/certs/
* TLSv1.2 (OUT), TLS header, Certificate Status (22):
* TLSv1.2 (OUT), TLS handshake, Client hello (1):
* TLSv1.2 (IN), TLS handshake, Server hello (2):
* TLSv1.2 (IN), TLS handshake, Certificate (11):
* TLSv1.2 (IN), TLS handshake, Server key exchange (12):
* TLSv1.2 (IN), TLS handshake, Server finished (14):
* TLSv1.2 (OUT), TLS handshake, Client key exchange (16):
* TLSv1.2 (OUT), TLS change cipher, Change cipher spec (1):
* TLSv1.2 (OUT), TLS handshake, Finished (20):
* TLSv1.2 (IN), TLS change cipher, Change cipher spec (1):
* TLSv1.2 (IN), TLS handshake, Finished (20):
* SSL connection using TLSv1.2 / DHE-RSA-AES256-SHA
* ALPN, server accepted to use http/1.1
* Server certificate:
* subject: C=US; ST=Washington; L=Seattle; O=Isilon Systems, Inc.; OU=Isilon Systems; CN=Isilon Systems; emailAddress=support@isilon.com
* start date: Apr 14 20:51:44 2022 GMT
* expire date: Jul 16 20:51:44 2024 GMT
* issuer: C=US; ST=Washington; L=Seattle; O=Isilon Systems, Inc.; OU=Isilon Systems; CN=Isilon Systems; emailAddress=support@isilon.com
* SSL certificate verify result: self signed certificate (18), continuing anyway.
> POST /platform/12/protocols/s3/mykeys HTTP/1.1
> Host: X.X.X.X:8080
> User-Agent: curl/7.79.1
> Accept: */*
> Cookie: isisessid=eyJhbGciOiJQUzUxMiJ9.eyJhdWQiOlsicGxhdGZvcm0iLCJuYW1lc3BhY2UiXSwiZXhwIjoxNjU1ODMzOTUzLCJpYXQiOjE2NTU4MTk1NTMsIm9uZWZzL2NzcmYiOiIxNDc2MmQyNi1lODA2LTQxYzEtYjMxMC00NDk3YWZiMjg5NTMiLCJvbmVmcy9pcCI6IjEyOC4yMjEuMjI3LjMzIiwib25lZnMvbm9uY2UiOjExMTUzNzgyODM1MTU4MjE5ODk0LCJvbmVmcy9zZXNzaW9uIjoiYmZkMjVhMTMtMDNlOS00OTdhLTk2OWYtYmEwZjU1YmFhZTAzIiwib25lZnMvdWEiOiJjdXJsLzcuNzkuMSIsIm9uZWZzL3ppZCI6MSwic3ViIjoiYXBleDAxIn0K.ioRleO4O9kqDcQfzDUpjKDA9bgnpqqSYPQWJ9sDRSfkL0xI1F29YpTvnoa3uKPLZ7pE8sedkk6vpPcif1Tb7L7-9t4fG2kIXJKK7vm1VNNStUFRQMHMc1vaf8UzKwwJJKf0S_3GltOo8iRK2fdkw_bigw2xOwIHr-85YCHGJeYdFiJ2pK_CI_zYPbGAeg5hJFV7Ylci9FDRI8SDElIBe8FrvaZuiPsMloRU8oL4dxco1jAfPhjsv3YOUDXTEq7kI3xCNkKIj5PtQMjQInDz4qxHVNo9Ks7uEm2cjYotNcQ424i0tuGTe2piwdvlaiEC6WaqKo7HhuPEYqQ7vmgK_seCEb9GY6wAXw9xhpfRHb38f2qDohZj17J-6TzKU32PZ9NJutAidTFIVKH01JGOPRRdPM9oex4VH7FUFDhPAGSng1nmBEx6wk10D1LjTB36UbSQ9lkrh7y84DLZYSlJAfo3iX1_w4bZ0tZHa51K13KedLb4E3Jafjkp-MOUUwMMbjXDgxoC0IRWc2HgilDnvKaSe7R8t9vogW0E5m-0jophQD70BY7UioNu-U6CnaoFojQ-yKFS3t6ZV8i40mD3XaZKS5oeePUFWmlmPFEugziuS4dTdQY-_Myei1RhQPRydp_xFUVZyBb79yv71FLtouqB3UY0zy0qiWDip6VRCphc%3D; isicsrf=14762d26-e806-41c1-b310-4497afb28953
> Content-type:application/json
> X-CSRF-Token: 14762d26-e806-41c1-b310-4497afb28953
> Referer:https://X.X.X.X
>
* Mark bundle as not supporting multiuse
< HTTP/1.1 201 Created
< Date: Tue, 21 Jun 2022 13:54:51 GMT
< Server: Apache
< Allow: GET, POST, DELETE, HEAD
< X-Frame-Options: sameorigin
< X-Content-Type-Options: nosniff
< Strict-Transport-Security: max-age=31536000;
< Content-Security-Policy: default-src 'self' 'unsafe-inline' 'unsafe-eval' data:; script-src 'self' 'unsafe-eval'; style-src 'unsafe-inline' 'self';
< Transfer-Encoding: chunked
< Content-Type: application/json
<
{
"keys" :
{
"access_id" : "1_apex01_accid",
"secret_key" : "<< SECRET KEY >>>",
"secret_key_timestamp" : 1655819691
}
}
* Connection #0 to host X.X.X.X left intact
apex7R33643-3%
受影响的产品
APEX, APEX Data Storage Services文章属性
文章编号: 000200704
文章类型: Solution
上次修改时间: 28 6月 2023
版本: 7
从其他戴尔用户那里查找问题的答案
支持服务
检查您的设备是否在支持服务涵盖的范围内。