IDPA: Security Vulnerabilities for Apache Tomcat Default Installation
Summary: The article provides a workaround for "Security Vulnerabilities for Apache Tomcat default installation and or welcome page installed" detected on ACM.
This article applies to
This article does not apply to
This article is not tied to any specific product.
Not all product versions are identified in this article.
Instructions
The following vulnerability might be detected on the ACM part of IDPA for Port 8543:
| Vulnerability Title | Components | Service Port | Vulnerability Severity Level | Vulnerability Description | Vulnerability Proof | Vulnerability Solution |
|---|---|---|---|---|---|---|
| Apache Tomcat default installation or welcome page installed | ACM | 8543 | 5 | The Tomcat default installation or "Welcome" page is installed on this server. This usually indicates a newly installed server which has not yet been configured properly and which may not be known about. Often, Tomcat is installed along with other applications and the user may not know that the web server is running. These servers are rarely updated and rarely monitored, providing hackers with a convenient target that is not likely to trip up any alarms. |
Running HTTPS service * Product Tomcat exists -- Apache Tomcat 9.0.45. HTTP GET request to https://<ACM IP>:8543/HTTP response code was an expected 200. <h1>Apache Tomcat/9.0.45</h1> 27: </div> 28: <div id="upper" class="curved container"> 29: <div id="congrats" class="curved container"> 30: ... this, you have successfully installed Tomcat. Congratulations!</h2> |
Change the default page, or stop and disable the Tomcat server completely. If this server is required to provide necessary functionality, then the default page should be replaced with relevant content. Otherwise, this server should be removed from the network, following the security principle of minimum complexity. |
Follow these steps to work around the issue:
- Log in as root to the ACM
- Change the working directory to
/usr/local/dataprotection/apache-tomcat-9.0.*/webapps/ROOT.
acm:~ # cd /usr/local/dataprotection/apache-tomcat-9.0.*/webapps/ROOT
In this example, the Apache Tomcat path is
/usr/local/dataprotection/apache-tomcat-9.0.45/webapps/ROOT
This could be changed depending on the IDPA version being worked on.
- Confirm that the
index.jspfile exists in the directory:
acm:/usr/local/dataprotection/apache-tomcat-9.0.45/webapps/ROOT # ls -la total 188 drwxr-x--- 3 idpauser idpauser 4096 Nov 12 00:29 . drwxr-x--- 6 idpauser idpauser 4096 Dec 6 17:00 .. -rw-r----- 1 idpauser idpauser 12243 Feb 4 2022 1 -rw-r----- 1 idpauser idpauser 6898 Mar 30 2021 RELEASE-NOTES.txt drwxr-x--- 2 idpauser idpauser 4096 May 7 2021 WEB-INF -rw-r----- 1 idpauser idpauser 27235 Mar 30 2021 asf-logo-wide.svg -rw-r----- 1 idpauser idpauser 713 Mar 30 2021 bg-button.png -rw-r----- 1 idpauser idpauser 1918 Mar 30 2021 bg-middle.png -rw-r----- 1 idpauser idpauser 1401 Mar 30 2021 bg-nav.png -rw-r----- 1 idpauser idpauser 3103 Mar 30 2021 bg-upper.png -rw-r----- 1 idpauser idpauser 21630 Mar 30 2021 favicon.ico -rw-r----- 1 idpauser idpauser 12243 Feb 4 2022 index.jsp -rw-r----- 1 idpauser idpauser 5542 Mar 30 2021 tomcat.css -rw-r----- 1 idpauser idpauser 67795 Mar 30 2021 tomcat.svg acm:/usr/local/dataprotection/apache-tomcat-9.0.45/webapps/ROOT #
- Make a backup of the existing
index.jspby copying it toindex.jsp.default:
acm:/usr/local/dataprotection/apache-tomcat-9.0.45/webapps/ROOT # cp -p index.jsp index.jsp.default
NOTE: For reference, before implementing the workaround, run the command
curl -kv https://localhost:8543. This output should be used in Step 8 to compare the output after the workaround.
- Create a new file called
index.jspand replace its content with the following:
<html>
<body>
<%
response.sendRedirect("../dataprotection/");
%>
</body>
</html>
Here is a simple procedure on how to create and edit the index.jsp file:
- Remove the existing
index.jsp
rm index.jsp
- Create a new
index.jspfile using the vi editor.
vi index.jsp
- Press
ito enter insert mode. This allows the edition to the file. - Copy the text above and paste it into the vi editor.
- Exit insert mode by pressing
Esc - Save the changes and exit vi by typing
:wq!and pressing Enter.
- Verify the contents of the
index.jspfile using the following commands:
acm:/usr/local/dataprotection/apache-tomcat-9.0.45/webapps/ROOT # ls -la
total 192
drwxr-x--- 3 idpauser idpauser 4096 Dec 6 17:05 .
drwxr-x--- 6 idpauser idpauser 4096 Dec 6 17:00 ..
-rw-r----- 1 idpauser idpauser 12243 Feb 4 2022 1
-rw-r----- 1 idpauser idpauser 6898 Mar 30 2021 RELEASE-NOTES.txt
drwxr-x--- 2 idpauser idpauser 4096 May 7 2021 WEB-INF
-rw-r----- 1 idpauser idpauser 27235 Mar 30 2021 asf-logo-wide.svg
-rw-r----- 1 idpauser idpauser 713 Mar 30 2021 bg-button.png
-rw-r----- 1 idpauser idpauser 1918 Mar 30 2021 bg-middle.png
-rw-r----- 1 idpauser idpauser 1401 Mar 30 2021 bg-nav.png
-rw-r----- 1 idpauser idpauser 3103 Mar 30 2021 bg-upper.png
-rw-r----- 1 idpauser idpauser 21630 Mar 30 2021 favicon.ico
-rw-r----- 1 idpauser idpauser 81 Feb 10 05:27 index.jsp
-rw-r----- 1 idpauser idpauser 12243 Feb 4 2022 index.jsp.default
-rw-r----- 1 idpauser idpauser 5542 Mar 30 2021 tomcat.css
-rw-r----- 1 idpauser idpauser 67795 Mar 30 2021 tomcat.svg
acm:/usr/local/dataprotection/apache-tomcat-9.0.45/webapps/ROOT # cat index.jsp
<html>
<body>
<%
response.sendRedirect("../dataprotection/");
%>
</body>
</html>
acm:/usr/local/dataprotection/apache-tomcat-9.0.45/webapps/ROOT #
- Open a web browser and access the ACM web page, and check if it is working correctly. When opening the ACM web page:
https://<ACM IP Adddress>:8543/
It should redirect automatically:
https://<ACM IP Adddress>:8543/dataprotection/#/login
- Validate the changes in the ACM command line:
Before implementing the workaround, the
curl -kv https://localhost:8543 would be similar to:
NOTE: The
curl -kv https://<ACM IP address>:8543 returns the same result:
acm:/usr/local/dataprotection/apache-tomcat-9.0.45/webapps/ROOT # curl -kv https://localhost:8543 * Rebuilt URL to: https://localhost:8543/ * Trying 12x.0.0.1... * TCP_NODELAY set * Connected to localhost (12x.0.0.1) port 8543 (#0) * ALPN, offering h2 * ALPN, offering http/1.1 * Cipher selection: ALL:!EXPORT:!EXPORT40:!EXPORT56:!aNULL:!LOW:!RC4:@STRENGTH * TLSv1.2 (OUT), TLS header, Certificate Status (22): * TLSv1.2 (OUT), TLS handshake, Client hello (1): * TLSv1.2 (IN), TLS handshake, Server hello (2): * TLSv1.2 (IN), TLS handshake, Certificate (11): * TLSv1.2 (IN), TLS handshake, Server key exchange (12): * TLSv1.2 (IN), TLS handshake, Server finished (14): * TLSv1.2 (OUT), TLS handshake, Client key exchange (16): * TLSv1.2 (OUT), TLS change cipher, Client hello (1): * TLSv1.2 (OUT), TLS handshake, Finished (20): * TLSv1.2 (IN), TLS change cipher, Client hello (1): * TLSv1.2 (IN), TLS handshake, Finished (20): * SSL connection using TLSv1.2 / ECDHE-RSA-AES256-SHA384 * ALPN, server did not agree to a protocol * Server certificate: * subject: C=US; ST=California; L=Irvine; O=EMC; OU=Avamar; CN=localhost.localdom * start date: Feb 4 12:27:16 2022 GMT * expire date: Feb 2 12:27:16 2032 GMT * issuer: C=US; ST=California; L=Irvine; O=EMC; OU=Avamar; CN=localhost.localdom * SSL certificate verify result: self signed certificate (18), continuing anyway. > GET / HTTP/1.1 > Host: localhost:8543 > User-Agent: curl/7.60.0 > Accept: */* > < HTTP/1.1 200 < Content-Type: text/html;charset=UTF-8 < Transfer-Encoding: chunked < Date: Fri, 10 Feb 2023 05:39:29 GMT < Connection: close < Server: DataDomain < <!DOCTYPE html> <html lang="en"> <head> <meta charset="UTF-8" /> <title>Apache Tomcat/9.0.45</title> <link href="favicon.ico" rel="icon" type="image/x-icon" /> <link href="tomcat.css" rel="stylesheet" type="text/css" /> <script>window.location = window.location.origin + "/dataprotection/"; </script></head> <body> <div id="wrapper"> <div id="navigation" class="curved container"> <span id="nav-home"><a href="https://tomcat.apache.org/">Home</a></span> <span id="nav-hosts"><a href="/docs/">Documentation</a></span> <span id="nav-config"><a href="/docs/config/">Configuration</a></span> <span id="nav-examples"><a href="/examples/">Examples</a></span> <span id="nav-wiki"><a href="https://wiki.apache.org/tomcat/FrontPage">Wiki</a></span> <span id="nav-lists"><a href="https://tomcat.apache.org/lists.html">Mailing Lists</a></span> <span id="nav-help"><a href="https://tomcat.apache.org/findhelp.html">Find Help</a></span> <br class="separator" /> </div> <div id="asf-box"> <h1>Apache Tomcat/9.0.45</h1> </div> <div id="upper" class="curved container"> <div id="congrats" class="curved container"> <h2>If you're seeing this, you've successfully installed Tomcat. Congratulations!</h2> </div> ... skipped </body> </html>
When the workaround has been implemented, the output should become:
acm:/usr/local/dataprotection/apache-tomcat-9.0.45/webapps/ROOT # curl -kv https://localhost:8543 * Rebuilt URL to: https://localhost:8543/ * Trying 12x.0.0.1... * TCP_NODELAY set * Connected to localhost (12x.0.0.1) port 8543 (#0) * ALPN, offering h2 * ALPN, offering http/1.1 * Cipher selection: ALL:!EXPORT:!EXPORT40:!EXPORT56:!aNULL:!LOW:!RC4:@STRENGTH * TLSv1.2 (OUT), TLS header, Certificate Status (22): * TLSv1.2 (OUT), TLS handshake, Client hello (1): * TLSv1.2 (IN), TLS handshake, Server hello (2): * TLSv1.2 (IN), TLS handshake, Certificate (11): * TLSv1.2 (IN), TLS handshake, Server key exchange (12): * TLSv1.2 (IN), TLS handshake, Server finished (14): * TLSv1.2 (OUT), TLS handshake, Client key exchange (16): * TLSv1.2 (OUT), TLS change cipher, Client hello (1): * TLSv1.2 (OUT), TLS handshake, Finished (20): * TLSv1.2 (IN), TLS change cipher, Client hello (1): * TLSv1.2 (IN), TLS handshake, Finished (20): * SSL connection using TLSv1.2 / ECDHE-RSA-AES256-SHA384 * ALPN, server did not agree to a protocol * Server certificate: * subject: C=US; ST=California; L=Irvine; O=EMC; OU=Avamar; CN=localhost.localdom * start date: Feb 4 12:27:16 2022 GMT * expire date: Feb 2 12:27:16 2032 GMT * issuer: C=US; ST=California; L=Irvine; O=EMC; OU=Avamar; CN=localhost.localdom * SSL certificate verify result: self signed certificate (18), continuing anyway. > GET / HTTP/1.1 > Host: localhost:8543 > User-Agent: curl/7.60.0 > Accept: */* > < HTTP/1.1 302 < Set-Cookie: JSESSIONID=3396A12A1A458BBB4DDCB636A72B66EE; Path=/; Secure; HttpOnly < Location: ../dataprotection/ < Content-Type: text/html;charset=ISO-8859-1 < Content-Length: 0 < Date: Fri, 10 Feb 2023 05:42:58 GMT < Connection: close < Server: DataDomain < * Closing connection 0 * TLSv1.2 (OUT), TLS alert, Client hello (1):
Additional Information
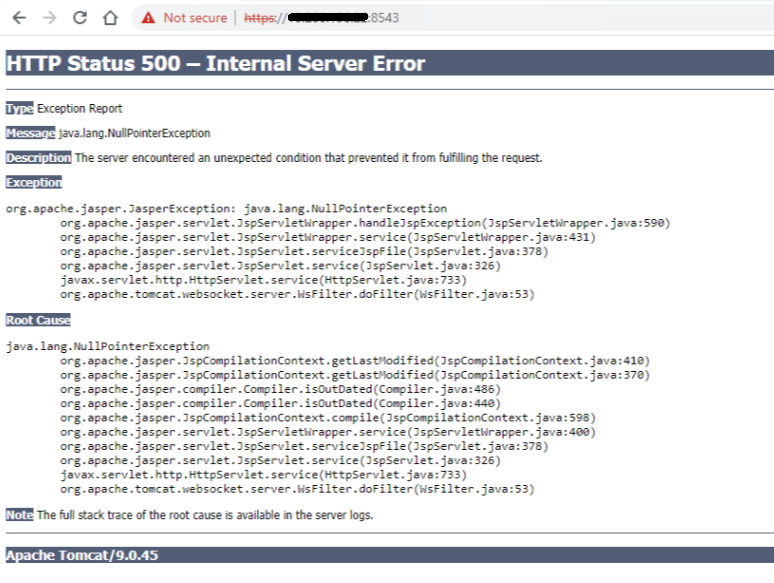
If the ACM web page shows an "HTTP Status 500 - Internal Server Error" after following the above procedure, for example:
Log in to the ACM using SSH as the root user, then restart the ACM service with the following commands:
service dataprotection_webapp stop service dataprotection_webapp start
Then reload the ACM web page again.
Contact Dell Support for further assistance if needed.
Affected Products
PowerProtect DP4400, PowerProtect DP5300, PowerProtect DP5800, PowerProtect DP8300, PowerProtect DP8800, PowerProtect Data Protection Software, Integrated Data Protection Appliance Family, Integrated Data Protection Appliance Software
, PowerProtect DP5900, PowerProtect DP8400, PowerProtect DP8900
...
Article Properties
Article Number: 000206114
Article Type: How To
Last Modified: 25 Aug 2025
Version: 11
Find answers to your questions from other Dell users
Support Services
Check if your device is covered by Support Services.