PowerEdge: What is the Default Username and Password for an Integrated Dell Remote Access Controller (iDRAC)
Summary: This article provides information about the iDRAC default credentials, and how to rest the password.
Instructions
PowerEdge, PowerFlex, VxRail, PowerVault, and others systems with an iDRAC are available with a few options regarding the password as it comes from the factory. The choices are Secure Default Password, Legacy Password, and Force Change Password.
Default IP address
After purchasing the server, you have the option to request a specific configuration for the iDRAC which would include specifying a set IP address. Alternatively you can select to have the default settings, where the default IP address would be 192.168.0.120.
Secure Default Password
By default, all PowerEdge servers ship with a unique, randomly generated iDRAC password, to provide additional security. This unique password is generated at the factory. It is located on the pull-out Service Tag on the front of the chassis, near the server asset tag. Customers who choose this option must write down this unique random password and use it to log in to iDRAC for the first time. For security purposes, Dell strongly recommends changing the default password.
Legacy Password
Customers who prefer the known legacy password "calvin" should choose this option. One reason to select this option would be to ensure conformance to current scripts. For security purposes, Dell strongly recommends changing the legacy password.
Customers should be aware that the known legacy username "root" is what they should be using the with legacy password.
Force Change Password
The Force Change of Password feature prompts the user to change the factory default password of the device. The Force Change Password screen appears after successful user authentication and cannot be skipped. Only after the user enters a password, normal access and operation will be allowed.
You can reset the password through the iDRAC settings by pressing F2 at startup. Also, you can reset the password to its factory default with the following racadm command:
racadm racresetcfg -all
To reset the password to the legacy password, use the following racadm command:
racadm racresetcfg -rc
Note: More tutorials about the iDRAC are available in the Dell article Support Articles for the iDRAC and the CMC.
What is the "Default Password Warning" on iDRAC? (SEC0701)
The default iDRAC username and password are widely known, and any user can access the server and make changes using the default credentials. The Default Password Warning feature in iDRAC warns you if the default login credentials are still in place.
Whenever a user with Configure User privileges logs in to iDRAC or SSH or Telnet or runs racadm commands remotely using the default login credentials, the system displays a warning message (SEC0701). Because UI and SSH or Telnet users log in once per session, they see a single warning message for each session. Because remote racadm users log in for every command, they see a warning message for every command.
An iDRAC with default login credentials is even less secure if the system is Internet-accessible or part of a large network with different trust boundaries. If any of the following items is configured, the possibility exists that iDRAC could become accessible on the Internet.
Whenever a user with Configure User privileges logs in to iDRAC using Web UI using the default login credentials, the Default Password Warning Message displays. From this page, the user can either change the password for a root user, or they can change nothing and continue logging in to iDRAC. The option to disable the Default Password Warning Message appears on this page if the user does not change the password.
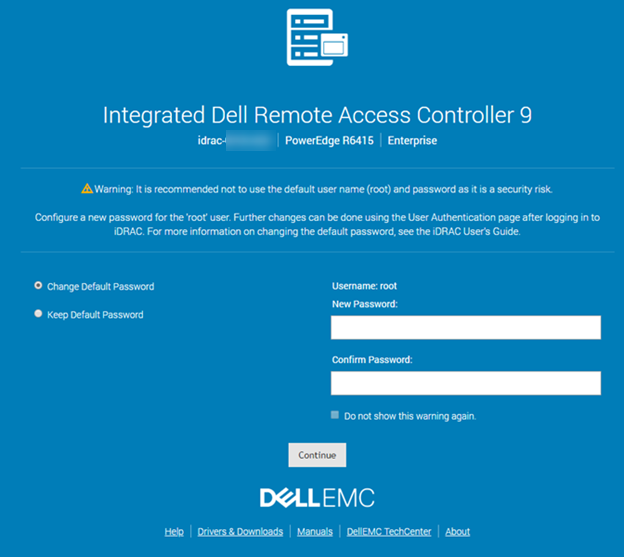
Figure 2: iDRAC9 default password warning
The Default Password Warning is enabled or disabled from the iDRAC Overview > iDRAC Settings > User Authentication > Local Users page, under the section titled Default Password Warning.
I cannot remember the iDRAC password
If you have lost the iDRAC password, you must reset the iDRAC to its default setting. This process is explained in article How to Reset the Integrated Dell Remote Access Controller (iDRAC)
How to Log in to iDRAC9 With the Default Password.
Duration: 00:00:54 (hh:mm:ss)
When available, closed caption (subtitles) language settings can be chosen using the Settings or CC icon on this video player.