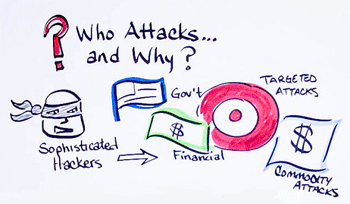
 As security threats become more insidious and pervasive, and data breaches more commonplace, network security must become an ongoing initiative that wraps security around and through the network, protecting from all perimeters. As BYOD, mobility, cloud computing, and Internet usage ramp up, a whole new generation of unknown threats is going to create a storm surge of risk to unsuspecting organizations of all sizes. Because we believed most organizations were unaware of these threats ─ and would be unable not only to detect, but also to combat them effectively ─ we commissioned research to determine where these threats lurk, how they are evolving and what organizations need to put in place to guard against them.
As security threats become more insidious and pervasive, and data breaches more commonplace, network security must become an ongoing initiative that wraps security around and through the network, protecting from all perimeters. As BYOD, mobility, cloud computing, and Internet usage ramp up, a whole new generation of unknown threats is going to create a storm surge of risk to unsuspecting organizations of all sizes. Because we believed most organizations were unaware of these threats ─ and would be unable not only to detect, but also to combat them effectively ─ we commissioned research to determine where these threats lurk, how they are evolving and what organizations need to put in place to guard against them.
We unveiled the survey findings, which do indeed show that many organizations are not ready to fight this fight. To provide some background, we commissioned Vanson Bourne, a reputable third-party research firm, to interview more than 1,440 global IT leaders across several different industries, in 10 countries. Survey respondents included IT leaders in all major industries ─ both public and private sector ─ in both mid-market and enterprise-size organizations.
Security breaches cost U.S. organizations billions of dollars annually, yet the survey results show that it takes too long for most respondents to detect a breach. This is compounded by the fact that many companies remain focused on external threats and don’t give enough credence to the unknown internal threats that can cause just as much damage to the network. Internal threats may be deliberate actions by some who have too much access to critical applications, or, in many cases, accidental ─ such as the transmission of unknown malware from a personal device when the device is used to access the network. Either way, the security gaps and vulnerabilities that exist both inside and outside the network, and on endpoints and devices, must be eliminated to ensure the safety of both corporate and customer data.
This is why we bolster our best-of-breed Connected Security solutions with the following set of best practices to help our customers and partners detect and mitigate these unknown threats:
- Implement a sound Identity and Access Management strategy ─ Add business agility with governance for users, data and privileged accounts
- Install Deeper Network Security – Leverage next-generation firewalls (NGFWs) that scan every byte of every packet – including SSL traffic to block threats before they enter the network, without compromising performance.
- Rely on Comprehensive Mobile Security ─ Protect organizational networks from mobile malware, rogue access, and other unknown threats by setting up central control over remote access points that strictly configures security policies to grant access only to trusted devices and authorized users.
- Deploy an All-Perimeter Defense ─ Connect your entire organization – data, users, endpoints and cloud— to detect and protect against all internal and external malicious behavior.
- Protect data wherever it goes – Employ data protection and encryption to safeguard against data loss, and lost or stolen organizational assets
- Fortify security with 24×7 protection – Augment existing security capabilities with managed security services, integrated threat intelligence and security and risk consulting to become more predictive about combating threats
The new generation of stealthy, elusive threats can dodge detection and nimbly circumvent network security controls, helping themselves to critical corporate data and inflicting huge headaches and a high price tag on unprepared organizations. Combined with Dell’s best practices, the capabilities of our comprehensive solution set prepare our customers to fight back with tight, connected security that governs access to every application and protects every device, on both sides of the network perimeter.
For more information about unknown threats, read the Dell press release; for complete details of the security survey, check out the white paper, “Protecting the organization against the unknown: A new generation of threats.”