Let Cybersecurity Awareness Month serve as yet another reminder that optimizing your unstructured storage and building out a modern cybersecurity strategy should go hand in hand to effectively defend your organization’s critical data. These massive collections of large files, graphics, videos and objects that are used to gather insights, determine trends, capture customer information and drive innovations for your organization are, not surprisingly, a profitable target for ransomware and cyberattackers.
Just take a look at the endless list of ransomware attacks in the news and you will see that most of them – from banks, hospitals and schools, to police departments – involve file data. So, while your unstructured data continues to grow at an enormous pace, accounting for more than 90 percent of the data created each year per recent IDC research, so will the interest from cyberattackers.
In an ocean of vendors making claims and talking about basic levels of ransomware protection, there is only one company – Dell Technologies – that has the experience to provide comprehensive solutions for securing your unstructured data. With Dell PowerScale, the world’s most cybersecure scale-out NAS¹, and Dell ECS, the world’s most cybersecure object storage² solution you can get ahead of the attackers and secure your unstructured data reliably for the long term.
While other vendors might say they offer enterprise cyber-protection and recovery solutions for file and object data, the reality is that the majority of these products are missing some key security features and focus mainly on recovery and very little on detection and prevention. Also, many of these vendors are of the opinion that offering immutable snapshots is sufficient to fully address cyberattacks.
At Dell we believe that implementing immutable snapshots is beneficial and is something we have been doing for years. Uniquely, Dell provides a tamper-proof clock so attackers cannot roll the clock forward – a technique used to “age out” the snapshots. But snapshots alone can leave you vulnerable. Above and beyond that, you need to look for a solution that offers comprehensive security features and a secure vault or air gap technology that can fully isolate data copy from the production environment before a cyberattack happens.
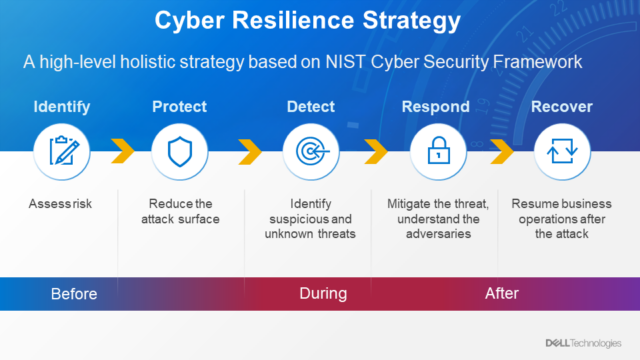
For customers looking to build a robust security framework, we recommend following a NIST Zero Trust architecture framework. With PowerScale and ECS you gain tools that can be used for each of the stages – Identify, Protect, Detect, Respond and Recover – that can be applied to all the data at once, regardless of where it is located.
PowerScale and ECS are designed for federal-grade security with a comprehensive, continuously enhanced set of security features. For example, with the modern architecture of PowerScale you can store all your unstructured data in a single, scalable data lake. To reduce risk to this data, PowerScale administrators only need to apply policies once to all of the data in a set-it-and-forget-it manner – unlike some of the other storage architectures out in the market that require policies be set to each individual data repository.
Security Features Built Into OneFS
The PowerScale OneFS operating system comes with a comprehensive set of security features including:
-
- Customizable role-based access control
- Access zones for data segregation
- Data at rest and data in flight encryption
- Virus scanning tools
- WORM SmartLock compliance
- Multi-protocol ACLs for cross protocol security and auditing
- External key manager for data at rest encryption
- STIG-hardened security profile
- Common Criteria certification
- Support for UEFI Secure Boot across PowerScale platforms
Additional cyber-resiliency tools are available for data isolation, automated threat detection and rapid recovery.
Our upcoming OneFS release will add security features such as software-based firewall, multi-factor authentication with support for CAC/PIV, SSO for administrative WebUI, USGv6R1 support and FIPS-compliant data in flight.
We also believe meeting the highest level of federal compliance is paramount to support industry and federal security standards. We are excited to announce that our scheduled verification by the Defense Information Systems Agency (DISA) for inclusion on the Department of Defense Information Network (DoDIN) Approved Product List will begin in March 2023. For more information on this, refer to the DISA schedule.
Our Unique Approach for Cyber-defense
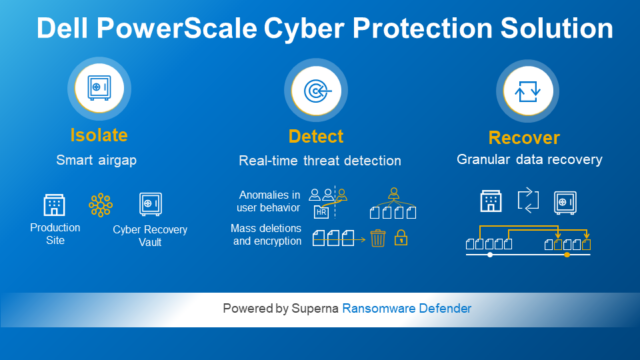
Three key components of a robust cyber protection and resiliency solution are based on the assumption that a breach is inevitable, meaning that a network separation needs to be a critical component of your cyber resiliency strategy. Advanced features in the PowerScale Cyber Protection Solution go beyond what other vendors on the market can offer to protect your data layer. It provides:
-
- Data isolation to a cyber vault that creates an air gapped copy of critical data from all internal and external network paths. Data placed in a cyber vault becomes the recovery copy of last resort.
- Intelligent detection based on AI-powered threat detection monitors data access for suspicious activity, such as anomalies in user behavior, mass deletions and encryption, and automated responses can block suspected users, suspend air gap activity and/or create additional snapshots for recovery.
- Rapid recovery with a single click failover provides ultra-fast access to the known clean copy in the Cyber Vault to restore data from the air gapped copy. A petabyte of data on PowerScale can be recovered within a few hours. No other value storage, on-premises or in the cloud, comes close to PowerScale’s data recovery speed.
Enhanced Cyber-protection and Recovery for Object Storage
Earlier this month, we announced a new cyber-protection solution for our scalable object storage platform ECS. Just as for PowerScale, this solution expands cyber-protection capabilities to help secure object data to an isolated cyber vault residing locally or in a remote environment.
Accessible through the AWS S3 protocol, critical applications and backup servers can continue to access the isolated copy while supporting legal compliance in the event of a cyberattack that compromises the primary and secondary data copy. Together with AI-powered threat detection and immutability, the new solution provides organizations a rapid path to data recovery from ransomware and other malicious attacks.
For more information on Dell’s unique end-to-end cybersecurity capabilities for both file and object data, explore our websites for PowerScale and ECS.
1 Based on Dell analysis comparing cybersecurity software capabilities offered for Dell PowerScale vs. competitive products, September 2022.
2 Based on Dell analysis comparing cybersecurity software capabilities offered for Dell ECS vs competitive products, September 2022.