

Launch
Quantum Resilience, Built In
Key takeaways: Quantum computing is accelerating enterprise risk, and PQC mandates are approaching quickly. Dell’s 2026 commercial PCs harden the boot chain with quantum‑resistant cryptography—protecting the root of trust, firmware and BIOS integrity—to help organizations align with emerging standards, strengthen foundational security, and begin the quantum transition with confidence.
Quantum computing is accelerating faster than most organizations expected. While its breakthroughs promise major advances in science, AI and industry, they also introduce a new class of security risks that can’t be addressed with today’s cryptographic standards. For CIOs, CISOs and IT leaders, this shift isn’t theoretical—it’s becoming a strategic priority for organizations to ensure strong security. Preparing early helps reduce risks well before large‑scale quantum computers reach the market.
Industry regulators, government agencies, and standards authorities agree: organizations must begin transitioning to post‑quantum cryptography (PQC) now. U.S. federal guidance, including CNSA 2.0 and OMB memos, points toward a series of authoritative milestones between 2025 and 2030, culminating in the exclusive use of quantum‑resistant algorithms for many systems. For many enterprises, this means the window to modernize cryptographic foundations—and the infrastructure that relies on them—can be deceptively shorter than a typical hardware refresh cycle.
In other words: preparation is not optional, and it is not a future IT problem. PQC readiness will require years of planning, inventory, testing, and coordinated upgrades across firmware, devices, applications, and networks. To meet the timelines ahead, organizations must start at the deepest layers of their infrastructure—layers that determine whether other security improvements can be trusted at all.

Getting your fleet quantum-ready
There’s a lot to do. Where do you start?
The quick answer: Your suppliers should be helping guide you.
As one of the world’s largest PC and infrastructure solution providers, Dell thinks about security a lot. We are aligning with emerging CNSA 2.0 standards, and we are well-positioned to help support your transition.
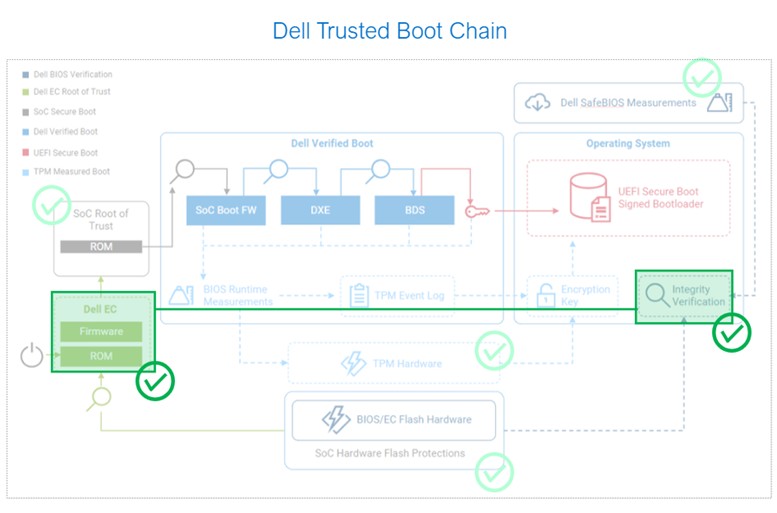
When it comes to PCs, we think about securing the system holistically, including during the earliest boot stages, which rely heavily on cryptography to provide a secure foundation for the rest of the system. If quantum‑enabled attackers were to compromise the foundational firmware or tamper with the root of trust, every other security measure—from identity tools to EDR—could potentially be undermined.
As announced today, Dell is prioritizing post-quantum upgrades for our commercial PCs with that in mind. We are:
-
- Strengthening the hardware root of trust with an upgraded embedded controller (EC): Because the EC verifies both its own integrity of the chipset and BIOS, enhancing its cryptographic strength provides a significantly stronger security. Any compromise at this stage could jeopardize the entire device, making this one of the most essential layers to futureproof early. Dell’s EC integrity verification now includes Leighton-Micali Signature (LMS) verification algorithms that are resistant to quantum computing hacks.
- Protecting the firmware supply chain with quantum-resistant code signing: Code (including firmware) signing is one of the most heavily targeted links in the supply chain. Attackers know that if they can steal signing keys or forge code signatures, they can deliver malicious firmware that looks authentic (learn more about cyber kill chains and the risk of firmware compromise here). Dell’s upgraded EC and BIOS signing now also use LMS verification preventing unauthorized signing—even in sophisticated attack scenarios. By modernizing the signing system itself, Dell ensures that every firmware update delivered to customer PCs is protected by cryptography designed for the coming quantum era.
- Upgrading BIOS-level tamper detections: The BIOS is a prime target for advanced attackers because traditional security tools struggle to see activity below the operating system. As we detailed earlier, Dell’s off‑host BIOS verification provides a unique safeguard by comparing BIOS measurements against golden images stored securely in Dell’s cloud. This upgraded countermeasure, now utilizing SHA-512, improves resilience to hash‑collision attacks—even those accelerated by quantum computing. By performing verification off the device and using PQC‑aligned algorithms, Dell provides a powerful early‑warning mechanism for tampering at one of the most sensitive layers of a PC.
Each upgrade strengthens a different link in the PC boot chain, anchoring the PC in stronger, more resilient cryptography. In this way, we protect the trust chain that organizations rely on throughout the lifetime of every device. (To learn more about Dell’s approach to PC security, check out our Below-the-OS Security Paper).
Secure by design = Quantum-safe by design
Dell’s new 2026 commercial PC portfolio supports all of these quantum‑threat‑resistant PC security features.
Again, these features weren’t chosen at random—they reflect the sequence required to modernize cryptography safely. Before organizations can adopt new algorithms for data, identity or network protection, they must first secure the trust chain that validates every boot and every security update. This foundation depends not only on strong firmware and silicon protections, but also on trusted, validated components throughout the supply chain.
By beginning at the foundation, Dell helps customers reduce risk, align with emerging PQC mandates and establish a more resilient path forward.
The quantum transition has begun. Dell’s latest commercial lineup helps provide essential first steps—clear, practical upgrades that help customers move from uncertainty to preparedness. If you’d like to learn more about our built-in security and how Dell can help you navigate the PQC migration, please reach out to our specialists.