

Endpoint Security
Why Choose Hardware-Assisted Security
Hybrid remote and cloud-based work increased the attack surface exponentially. We went from employees sitting in offices within the safety net of enterprise security to a distributed workforce. All kinds of endpoint devices are now connecting to corporate networks and clouds from everywhere. And attackers are seeing the opportunities.
It’s not just endpoint devices about which we need to worry. Attacks can also originate in the network and the cloud, too. Attackers are directing their efforts to the organization’s entire computing stack, blending in with valid system processes. They’re taking advantage of the fact that areas of the device—for example, the firmware—have traditionally lacked visibility and observability. In some cases, attackers can bypass legacy detection software you have in place (e.g., traditional antivirus, endpoint detection and response (EDR)) completely undetected. Another example is fileless malware attacks in memory—now a primary method attackers use to circumvent traditional signature and behavior-based approaches.
This is terrifying, especially given most organizations are not prepared for these types of persistent and emerging attacks.
This is why Dell, Intel and CrowdStrike teamed up to orchestrate hardware-assisted security.
What do we mean by “hardware-assisted security?” Simply put, this is hardware and software security integrated to bring greater visibility and actionability to your fleet. Let’s break down the different technologies at play that power hardware-assisted security.
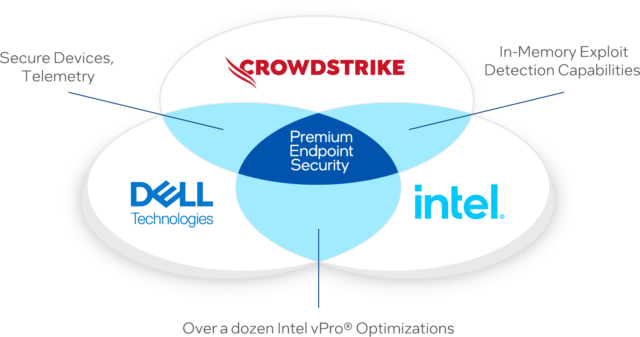
Dell Technologies. The integration is centered around Dell Trusted Devices, the industry’s most secure commercial PCs.* Dell commercial devices feature “built-in” hardware and firmware security to prevent and detect foundational attacks at the BIOS, firmware and hardware levels (e.g., SafeBIOS Indicators of Attack and off-host BIOS verification), all designed to mitigate the risk of compromise when the device is in use.
Importantly, the solution leverages Dell hardware-level telemetry to improve time to detection of some of the stealthiest attacks like those targeting the firmware. In fact, Dell is the only PC manufacturer that integrates this tamper/threat detection telemetry at the device-level with software to improve fleet-wide security.*
Intel. There are two sets of Intel vPro security features that Dell and CrowdStrike leverage. First, Dell commercial PCs harness several Intel vPro protections collectively called Intel Hardware Shield to bolster device-level security, including BIOS Guard and Boot Guard. With Intel vPro device features enabled, Dell provides secure off-host firmware verification for the Intel Management Engine (ME), a feature that is exclusive to Dell commercial devices.*
For the second set of protections, Intel Threat Detection Technology leverages the integrated GPU available on most Intel client systems to offload critical memory scanning functionality. CrowdStrike uses this advanced memory scanning (AMS) to find suspected malware patterns in memory to detect fileless attacks.
CrowdStrike. The CrowdStrike Falcon® platform is the (“built-on”) cybersecurity software layer that sits on top of these integrated hardware solutions, strengthening the security of any fleet of devices by delivering advanced AI-native protection. The Falcon platform adds several key capabilities. We already talked about AMS above. Then, there’s hardware enhanced exploit detection (HEED), which looks for other similar memory use exploitation and redirects execution to an attacker-controlled location. CrowdStrike Falcon® Insight XDR delivers immediate value with its industry-leading endpoint security platform based on indicators of attack (IOAs), allowing organizations to minimize their efforts spent handling alerts by reducing time to detect, investigate and respond to attacks. Falcon Insight XDR provides visibility and in-depth analysis of your endpoints and beyond, automatically detecting suspicious activity and stopping stealthy attacks and potential breaches.
Finally, bringing this back full circle, there’s Dell device-level telemetry (i.e., security notifications and alerts), which allows CrowdStrike Falcon to tap into additional vulnerability data “below the operating system” to enable swift, effective threat detection, analysis and response.
Multiple layers of security help mitigate the risk of an attack getting through. Our integrated hardware and software security solution takes it to the next level. With Dell, Intel and CrowdStrike in place, customers can:
-
- Shrink the attack surface by having solutions work together versus in silos
- Enhance threat detection by weaving in hardware telemetry
- Maintain better policy compliance and device trust as they proceed on their Zero Trust journey
- Take full advantage of the efficiencies that come from consolidating security providers
Organizations are working hard to shore up their defenses, but attackers are highly motivated. The average potential payout for just a single successful breach is massive—estimated to be $4.4 million in 2023.¹ The consequences—both financial and reputational—are too great to leave gaps in your security ecosystem. That said, you don’t need every security tool out there. You need the right ones—ones that talk to each other. As experienced IT and security partners, Dell, Intel and CrowdStrike understand the security challenges organizations face and proactively try to solve for them. We saw the gap and collaborated to bring hardware-assisted security to the market. Read our Solution Brief or watch the LinkedIn Live broadcast on demand to learn how hardware-assisted protections can enhance your security posture. As always, our security specialists are here to help.
*Based on Dell internal analysis, September 2023. Applicable to PCs on Intel processors. Not all features available with all PCs. Additional purchase required for some features.
1 IBM Report: Half of Breached Organizations Unwilling to Increase Security Spend Despite Soaring Breach Costs
